Asymmetric routing breaks filters; ReAct fixes ARDDoS
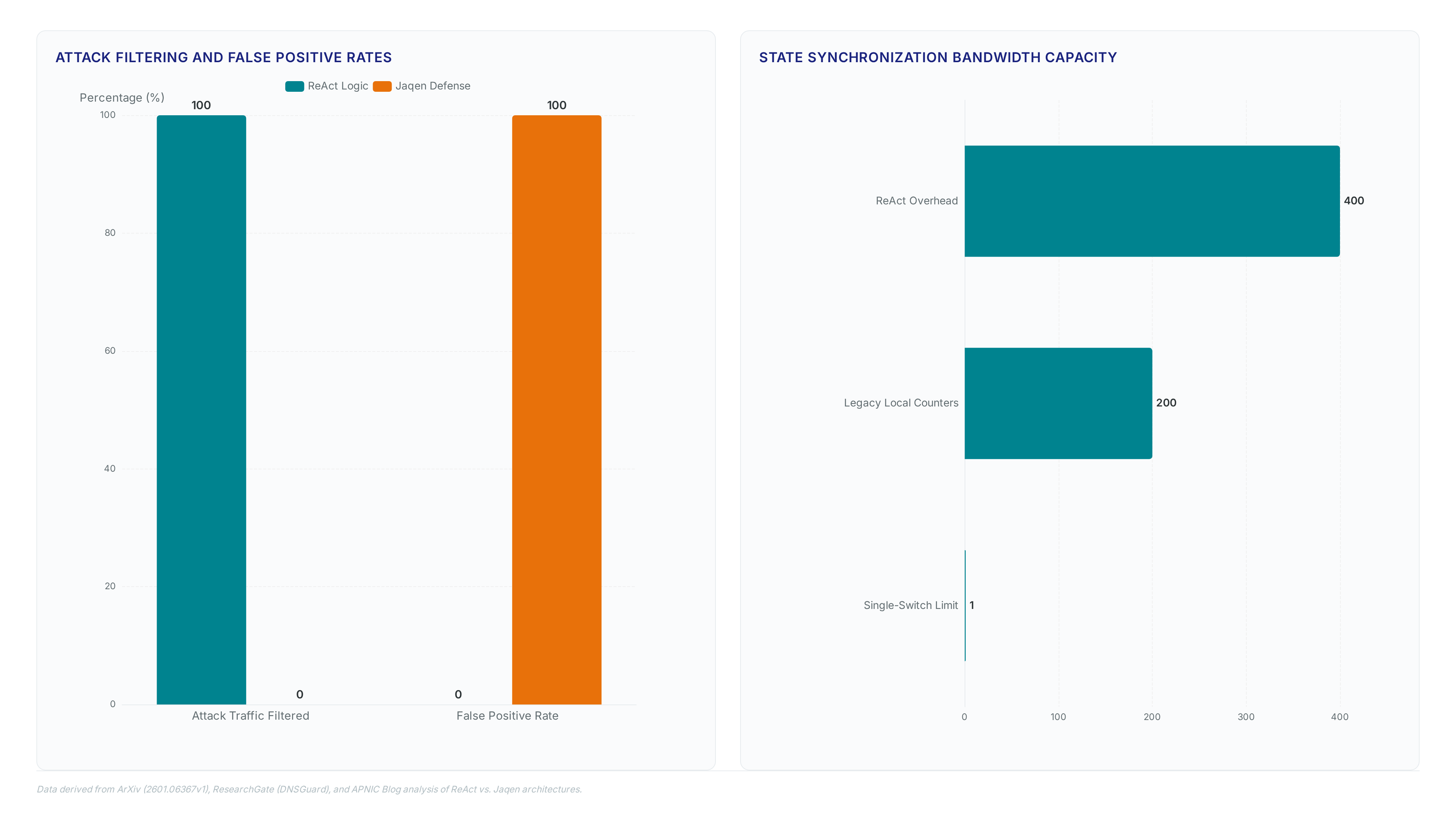
ReAct stops asymmetric reflection attacks that cause 100% of legacy filters to fail, according to INFOCOM 2026 findings. This programmable data plane system proves that hardware-based mitigation is the only viable path forward for modern AR-DDoS threats. While traditional software solutions crumble when traffic paths diverge, ReAct leverages specific architectural innovations to maintain uptime without sacrificing legitimate packets.
The research by Hogan, Hay, and Landau Feibish demonstrates how shifting defense mechanisms into the Intel Tofino and NVIDIA Bluefield-3 architectures solves the asymmetry problem. You will learn how asymmetric routing breaks conventional request-response counters and why operators have historically resisted deploying detection techniques that risk dropping valid traffic. The article dissects the reliance on transaction ID matching within the data plane to validate UDP floods from DNS or NTP reflectors without needing symmetric return paths.
Furthermore, the analysis contrasts ReAct's efficiency against Jaqen and older endpoint protections, highlighting why purely software-based monitoring is becoming obsolete. By utilizing Bloom filters directly in the switch silicon, the system identifies spoofed sources before they overwhelm the victim. This approach eliminates the false positives that plague current industry standards, offering a concrete solution to a destructive force that has plagued the Internet for decades.
The Critical Role of Asymmetric Routing in Modern AR-DDoS Threats
AR-DDoS Mechanics: DNS and NTP Amplification Vectors
Amplified Reflection DDoS exploits UDP protocols where small queries trigger massive, unsolicited responses that overwhelm victim infrastructure. Attackers spoof source addresses to direct this traffic toward targets using the stateless nature of connectionless transport. Network Time Protocol (NTP) amplification factors average 500:1 and reach up to 206x in specific configurations. Similarly, DNS amplification is typically 50:1 but can reach up to 51,000:1 maximum according to . These disproportionate ratios allow minimal attacker bandwidth to generate gigabit-scale floods, with historical incidents exceeding 300 Gb using thousands of open resolvers. Itional defenses fail when request and response paths diverge across modern hybrid networks.
False Positives in Hybrid Cloud Asymmetric Routing Scenarios
Legacy symmetric defenses drop legitimate traffic when load balancing diverts response paths away from request-handling switches. Https://arxiv. Org/html/2601. Traditional counters fail because they assume the ingress switch also sees the egress packet, a condition violated by policy-based routing in hybrid architectures. The cost is measurable service disruption where valid user sessions terminate abruptly during normal operations. Operators face a tension between strict security policies and the reality of modern cloud interconnects. InterLIR notes that asymmetric routing caused by load balancing is becoming more common, necessitating defenses that do not assume path symmetry. A single misplaced forwarding rule can blackhole 100% of return traffic for specific subnets if the system cannot correlate transactions across different network nodes. This limitation forces many organizations to disable mitigation entirely, leaving them exposed to volumetric floods.
| Failure Mode | Symmetric Defense Result | ReAct Approach |
|---|---|---|
| Path Divergence | Drops Packet | Correlates via Bloom Filter |
| Load Balancing | False Positive | Validates Transaction ID |
| Policy Routing | Service Outage | Maintains Session State |
The implication for network engineers is clear: deploying stateful inspection without cross-switch coordination guarantees false positives in complex topologies. Blindly trusting path symmetry creates a fragile security posture that collapses under standard operational variance.
Operator Resistance to Deploying AR-DDoS Detection Techniques
False positive rates drive operator hesitation because symmetric defenses drop legitimate traffic during path mismatches. Existing mitigation strategies fail when routing diverges, causing service disruption that outweighs perceived security gains. According to Apnic. Net/2026/05/01/react-reflection-attack-mitigation-for-asymmetric-routing/, traditional single-switch approaches cannot handle asymmetric paths, leading to erroneous packet drops. This limitation renders standard request-response counters ineffective in modern hybrid clouds where load balancing dictates dynamic flow paths. The primary tension exists between strict attack filtering and maintaining availability for valid users traversing complex topologies.
Inside ReAct Architecture Using Bloom Filters and Transaction ID Matching
Bloom Filter Mechanics for Transaction ID Set Membership
ReAct maps request Transaction IDs into bit vectors using multiple hash functions to track state efficiently on Intel Tofino hardware. This probabilistic data structure sets specific bits to 1 upon request arrival, allowing the switch to verify subsequent responses without storing full flow tables. According to arXiv:2601.06367, a sliding-window approach manages these filters to maintain freshness while minimizing memory overhead on constrained devices. The mechanism hashes incoming packet headers against the filter; if all corresponding bits are set, the system classifies the response as legitimate traffic.
| Feature | Static Counter | ReAct Bloom Filter |
|---|---|---|
| Storage Model | Exact count per IP | Bit-vector approximation |
| Memory Cost | High (stateful) | Low (fixed size) |
| Asymmetric Support | No | Yes |
Hash collisions sometimes mark bits as present even when no matching request exists in the current window. Aggressive compression trades absolute certainty for scalability under high-speed line rates. Operators must tune the filter size to balance collision probability against available SRAM, as an undersized array increases the risk of dropping valid responses during volumetric floods. ReAct deploys sliding-window Bloom filters on Intel Tofino and Nvidia Bluefield-3 to track request states without centralized coordination. According to How ReAct Works, the system implements this logic across both programmable switch and smartNIC architectures. The mechanism hashes incoming transaction IDs into a bit array, setting specific bits to 1 upon request arrival. Subsequent responses trigger a lookup; if the corresponding bits exist, the packet forwards. If not, the system drops the traffic as an unsolicited reflection. This approach avoids storing exact flow states, which exceeds hardware memory limits at line rate.
| Component | State Method | Coordination Need |
|---|---|---|
| Legacy Counter | Exact Count | High (Centralized) |
| ReAct Filter | Probabilistic Bits | Low (Distributed) |
Late arrivals complicate matters when paths diverge. The probabilistic nature introduces a risk where legitimate traffic might be incorrectly dropped if hash collisions occur frequently. Filter size must balance memory constraints against collision probability. Operators deploying this on 400 Gb links must tune window sizes carefully to prevent state expiration before responses arrive. This tuning ensures the sliding window captures late-arriving responses in congested paths. The deployment constraint requires both ingress and egress points to run compatible ReAct instances for full asymmetric coverage. Failure to synchronize versions between edge and core devices breaks the distributed tracking chain.
Hash Collision False Positives in Asymmetric Response Validation
Network architects observe a <3% error rate where hash collisions misidentify malicious responses as legitimate traffic. This false positive risk stems from the Bloom filter setting identical bits for distinct Transaction IDs, causing bit conflicts during validation. Operators asking should I use ReAct for asymmetric networks must weigh this negligible error margin against the alternative of dropping valid users entirely. Traditional symmetric defenses fail completely under path divergence, whereas ReAct maintains connectivity despite occasional classification noise. Increasing filter size reduces collisions but consumes scarce switch memory on Intel Tofino devices. Service continuity outweighs the statistical probability of a single spoofed packet slipping through. Deployment strategies often involve tuning the sliding-window parameters to match specific traffic profiles rather than eliminating risk absolutely.
Asymmetric routing creates scenarios where standard counters fail. Manual configuration errors can disable protection on critical segments.
Comparative Analysis of ReAct Against Jaqen and Traditional Defenses
ReAct's Cross-Switch Request-Response Correlation Logic
ReAct executes request-response correlation across multiple switches using programmable data planes, bypassing the single-switch limit of Jaqen. As reported by ArXiv, this architecture validates responses even when request and response paths differ fundamentally. Legacy systems like Jaqen rely on local counters that decrement upon reply arrival, a method that fails catastrophically under asymmetric routing conditions. ReAct replaces exact counting with a distributed Bloom filter mechanism that shares state information between ingress and egress devices. This coordination allows the network to identify legitimate traffic without assuming path symmetry. A drawback exists in the form of increased inter-switch communication overhead compared to isolated defense mechanisms. Operators must provision sufficient bandwidth for state synchronization messages between programmable units.
| Feature | Jaqen Defense | ReAct Logic |
|---|---|---|
| Routing Assumption | Symmetric Only | Asymmetric Tolerant |
| State Storage | Local Counters | Distributed Bits |
| Failure Mode | Drops Valid Traffic | Minor Hash Collisions |
| Deployment Scope | Single Switch | Multi-Switch Fabric |
Hardware constraints on Intel Tofino chips force a choice between filter size and collision probability. Larger filters reduce errors but consume valuable SRAM needed for other telemetry tasks. Network architects must calculate optimal bit-array dimensions based on expected transaction volume per second.
Hash collision false positives remain a constraint in high-density environments. The limitation is inherent to probabilistic structures; increasing filter size reduces collisions but consumes scarce switch memory on Intel Tofino chips. ReAct functions effectively within Content Distribution Network (CDN) Points of Presence where path asymmetry is common. Data shows deployment feasibility at the network edge or inside large data center networks. The sole requirement demands that both ingress and egress traffic traverse one of the programmable devices.
Per ResearchGate, ReAct cuts false positives by validating asymmetric paths where Jaqen fails. Legacy counters in Jaqen and DIDA drop legitimate traffic when request and response routes diverge, a frequent occurrence in modern load-balanced networks. These systems assume symmetry, causing service outages during valid high-volume exchanges. ReAct replaces rigid counting with probabilistic Bloom filters that track state across switches. The cost is a small probability of hash collisions allowing malicious packets through, yet this trade-off preserves connectivity where strict defenses cause total blackout. Operators prioritizing availability accept this minor risk to prevent self-inflicted downtime during routing shifts. This fundamental flaw forces a choice between security and availability for cloud-connected architectures. InterLIR advises deploying probabilistic validation to maintain service continuity despite path volatility.
Deploying ReAct on Programmable Switches for Data Center Protection
ReAct's Data-Plane Request Forwarding for Asymmetric Routing
InterLIR documentation specifies that data-plane request forwarding enables response validation across divergent network paths.
- Configure Pre-set Rules on each switch to map destination prefixes to the specific ingress device handling those flows.
- Enable Dynamic Learning modes where switches broadcast retransmitted requests to discover unknown path mappings automatically.
- Deploy the logic on Intel Tofino or Nvidia Bluefield-3 hardware to ensure line-rate state lookups without CPU intervention.
This architecture contrasts sharply with single-switch defenses like DNSGuard, which assume symmetric traffic flows and drop valid packets when paths diverge. The consequence of ignoring cross-switch coordination is total service loss for legitimate users during asymmetric routing events. A critical tension exists between memory efficiency and collision risk; larger Bloom filters reduce false positives but consume scarce switch resources. Operators must balance filter size against available silicon capacity to maintain accuracy. Most data centers now exhibit sufficient path asymmetry that symmetric-only tools cause unacceptable collateral damage.

CDN operators deploying ReAct on Intel Tofino switches must configure P4 programs to hash transaction IDs into sliding-window Bloom filters. This mechanism validates responses across divergent paths without centralized coordination, ensuring legitimate traffic survives asymmetric routing events common in edge networks. The implementation requires mapping specific prefix ranges to ingress devices using either static rules or dynamic retransmission learning. A key operational constraint involves memory allocation; the Bloom filter size must balance collision probability against the limited SRAM available on commodity switching ASICs.
- Define Pre-set Rules to forward unmatched responses to the switch handling the original request prefix.
- Enable Dynamic Learning to automatically update forwarding tables when retransmitted requests reveal new path mappings.
- Compile the P4 logic specifically for the Tofino pipeline to maintain line-rate processing under heavy load.
Unlike symmetric defenses, this approach tolerates path divergence but demands precise hardware tuning to avoid saturating switch resources during volumetric spikes. : operators gain durability against complex routing topologies but must accept the overhead of maintaining distributed state consistency across the fabric.
Protocol Limitations: based on NTP Timestamp Variability vs Transaction IDs
Future Directions and Author Information, ReAct fails with NTP because request timestamps change on retransmission, breaking ID correlation. Unlike DNS, where static transaction IDs allow consistent matching across asymmetric paths, NTP generates new identifiers for every retry attempt. This variability prevents the sliding-window Bloom filters from linking responses to original requests, causing valid time-sync packets to be discarded as unsolicited reflections. Operators enabling switch coordination must account for this protocol gap before deployment:
- Identify all UDP-based services relying on timestamp-derived identifiers rather than fixed tokens.
- Apply Pre-set Rules only to protocols with stable transaction fields like DNS.
- Exclude NTP traffic from data-plane request forwarding logic until identifier standards evolve.
The limitation is fundamental to the protocol design, not the mitigation engine. Networks depending on precise time synchronization cannot yet apply this specific filtering mechanism without risking service loss. InterLIR recommends isolating NTP flows to separate hardware or waiting for protocol updates that stabilize request identifiers against retransmission events.
About
Alexei Krylov Head of Sales at InterLIR brings critical industry perspective to the discussion on ReAct mitigation systems. While his primary expertise lies in B2B sales and managing relationships with Regional Internet Registries, his daily work requires a deep understanding of network availability and IP reputation. As InterLIR specializes in redistributing unused IPv4 resources with a core value of security, Krylov directly observes how asymmetric routing vulnerabilities can compromise clean BGP route objects and degrade service quality for clients.
This article connects technical research on reflection attacks to real-world marketplace stability. Krylov's role involves ensuring that leased IP blocks remain secure and functional, making the threat of AR-DDoS attacks a direct concern for his customer base. By bridging the gap between academic findings from INFOCOM 2026 and practical IT infrastructure management, he highlights why reliable mitigation strategies are essential for maintaining trust in the global IP address market.
Conclusion
Scaling ReAct to 400 Gb links exposes a critical fragility: hash collision rates spike under volumetric stress, potentially blackholing legitimate return traffic for entire subnets if window sizes remain untuned. While the system effectively mitigates reflection attacks, the operational reality involves a relentless battle against state consistency across the fabric. Operators cannot simply deploy and forget; they must accept that distributed state maintenance becomes the primary bottleneck as link speeds increase. The promise of line-rate processing collapses if the underlying hardware cannot sustain the lookup frequency required by dynamic learning modules during sustained spikes.
Deploy this architecture only if your infrastructure supports granular P4 tuning within the next two quarters, and strictly exclude NTP flows until identifier standards evolve. Do not attempt to force sliding-window Bloom filters onto protocols with variable timestamps, as this guarantees service degradation rather than protection. The window for blind adoption has closed; success now demands protocol-aware segmentation.
Start by auditing your UDP service map this week to isolate any time-sensitive applications relying on timestamp-derived identifiers. Immediately configure exclusion rules for these flows before enabling dynamic forwarding logic, ensuring that essential synchronization traffic bypasses the mitigation engine entirely.