Dynamic BGP fixes static route limits on AWS
Stop relying on manual failover when dynamic BGP routing automates recovery for up to 5,000 advertised routes on Transit Gateways. This migration is no longer optional for serious infrastructure, as dynamic routing has become the mandatory standard for enterprises connecting more than five branches to the cloud by 2027. While static configurations limit you to just 1,000 outbound routes and demand human intervention during outages, switching to Border Gateway Protocol unlocks automatic path selection and reliable liveness detection that static tunnels simply cannot match.
You will learn why clinging to static paths creates single points of failure in modern hybrid architectures and how IPSec tunnels paired with BGP eliminate the latency of manual rerouting. The analysis dissects the architectural superiority of route-based VPNs over policy-based legacy models, highlighting how automatic route propagation reduces operational overhead compared to managing hundreds of static entries. We examine specific data showing how dynamic setups support significantly higher route limits and enable Equal-Cost Multi-Path (ECMP) forwarding for aggregated bandwidth.
Finally, the guide provides a concrete, step-by-step migration strategy for moving from Virtual Private Gateways to AWS Transit Gateway without dropping active connections. You will see exactly how to reconfigure customer gateway devices to accept dynamic advertisements and verify tunnel health using native AWS tools. This transition ensures your network topology scales efficiently while adhering to the strict availability requirements demanded by current enterprise workloads.
The Strategic Role of Dynamic BGP Routing in Modern Cloud Infrastructure
Border Gateway Protocol (BGP) peering on AWS Site-to-Site VPN dynamically exchanges routes between AWS and on-premises gateways. Dynamic routing replaces manual static entries with automatic path updates, enabling networks to adapt instantly to topology changes without operator intervention. This mechanism relies on Border Gateway Protocol (BGP) sessions running over IP Security (IPSec) tunnels to propagate reachability information between the Virtual Private Gateway and customer endpoints. Data from Aws. Amazon. Com/whitepapers/latest/aws-vpc-connectivity-options/aws-site-to-site-vpn.
Scaling Enterprise Networks with Dynamic BGP Route Propagation
Transit Gateway supports 1000 dynamic routes versus 100 for static configurations. Dynamic route propagation eliminates manual updates by pushing on-premises prefixes directly into VPC route tables upon session establishment. This mechanism relies on Border Gateway Protocol (BGP) keepalives to detect upstream failures quicker than static tunnel status checks. Operational complexity increases because engineers must manage AS numbers and filter policies rather than simple IP entries. Networks exceeding five branches face exponential management overhead without this automation capability.
InterLIR analysis indicates that static scaling fails when route counts approach gateway limits, forcing architectural redesigns. Dynamic scaling allows organizations to add sites without reconfiguring core AWS endpoints. The limitation is the requirement for deeper protocol expertise during troubleshooting windows. Operators lose the predictability of fixed paths in exchange for durability against link flaps.
| Feature | Static Limit | Dynamic Limit |
|---|---|---|
| VGW Inbound | 100 routes | 100 routes |
| TGW Inbound | 100 routes | 1000 routes |
| Failover Speed | Manual/Slow | Automatic/Fast |
| Topology Fit | Single Site | Multi-Site |
Migration becomes mandatory when static entries consume available table space or when failover times exceed service level agreements. Large enterprises cannot sustain manual intervention for every branch office addition. The shift from hardware appliances to cloud-native connectivity drives this architectural necessity. By 2027, BGP over IPsec is projected to be the standard norm for enterprise networks connecting more than five to ten branches to the cloud. Ignoring this transition locks networks into fragile, unscalable designs.
Static vs Dynamic Routing: OpEx Trade-offs and Tunnel Failure Responses
Static routing mandates manual route table edits for every network change, directly inflating operational expenditure over time. Choosing the Right Routing Model: Static vs. Dynamic routing eliminates this friction by automating prefix advertisement, whereas static models trap engineers in repetitive configuration cycles. The architectural tension lies between initial simplicity and long-term maintainability; small networks benefit from zero-protocol overhead, but scaling introduces unacceptable human error risks.
Tunnel failure response times degrade notably without BGP keepalives to signal upstream path loss immediately. Operators relying on basic tunnel status often experience delayed convergence because the underlying link remains up while the remote peer is unreachable. This latency gap forces traffic blackholing until manual intervention occurs. Migrating to Border Gateway Protocol (BGP) shifts the failure domain from human reaction time to protocol timers, ensuring sub-second detection capabilities. The constraint requires staff proficiency in BGP attributes rather than simple IP entries. Networks ignoring this shift face compounding OpEx penalties as route counts grow. Strategic adoption of dynamic protocols reduces the mean time to recovery by removing the operator from the critical failover path.
Inside AWS Site-to-Site VPN Architecture and BGP Data Flow Mechanics
BGP Session Establishment and Route Propagation Mechanics
BGP session activation on AWS Site-to-Site VPN requires simultaneous IPsec tunnel stability and valid ASN configuration to propagate routes. The customer gateway must terminate both protocols concurrently, as the Virtual Private Gateway rejects route advertisements if the underlying security association is not fully established. AWS documentation confirms that static entries only populate route tables when connection status reads "UP," whereas dynamic prefixes flow based on real-time BGP session state.
- Configure the on-premises device with the assigned AWS ASN and peer IP addresses.
- Establish the IPsec tunnel to create the transport layer for TCP port.
- Verify the FSM reaches the Established state to trigger automatic VPC route updates.
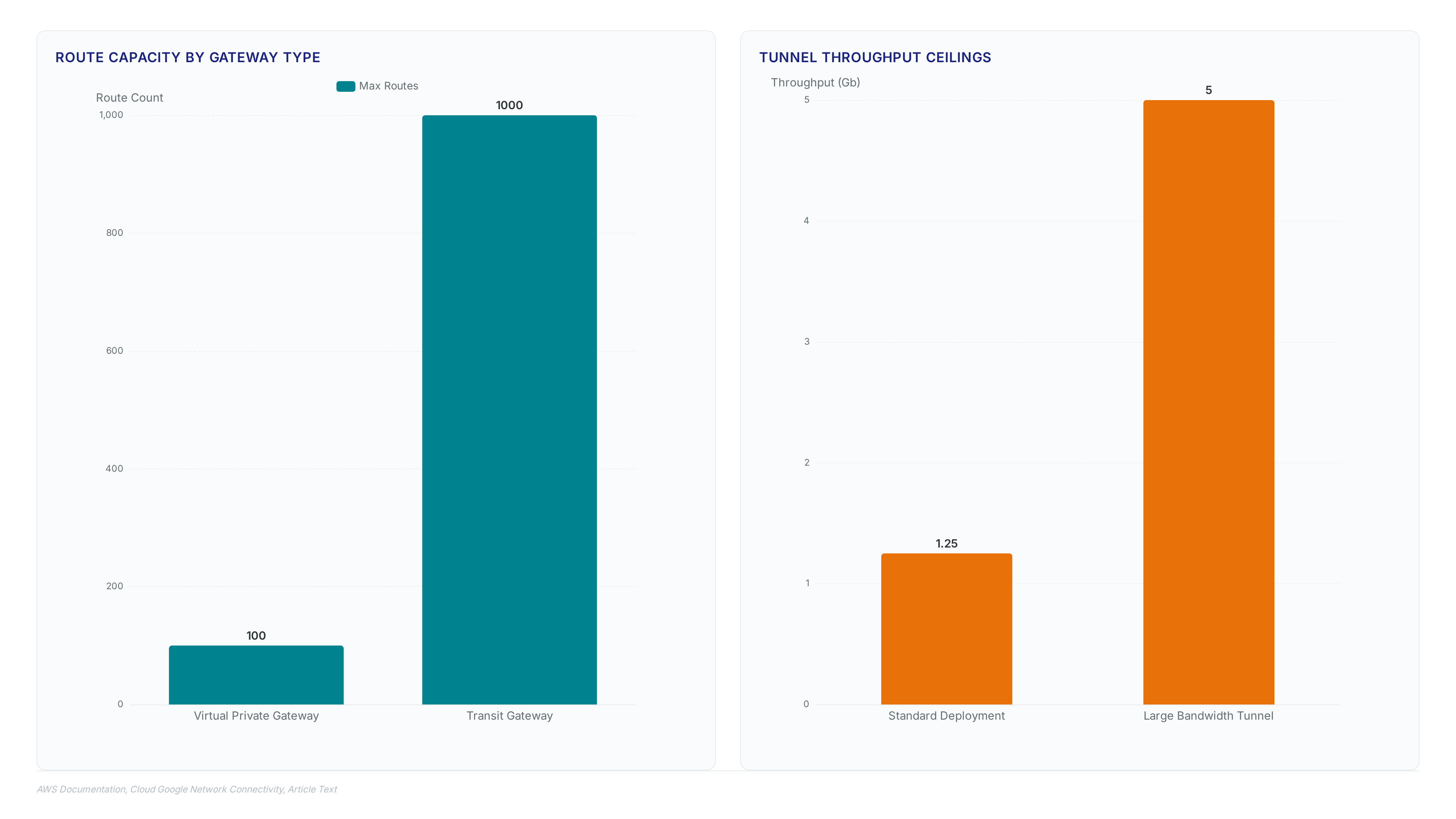
This sequence enables automatic failover because the protocol detects upstream silence quicker than static timers allow. However, the operational cost involves mastering complex attributes like AS paths and community strings instead of simple prefix lists. Networks relying on single-tunnel architectures cannot use ECMP to aggregate bandwidth beyond the standard 1.25 Gb limit per flow.
| Trigger | Tunnel Status UP | Session Established |
|---|---|---|
| Updates | Manual Edit Required | Automatic Propagation |
| Failover | Slow/Manual | Instant Detection |
The hidden tension exists between security strictness and routing agility; tight prefix filters prevent leaks but may block legitimate path changes during outages. Operators must balance these constraints to maintain availability without exposing the network to unauthorized route injections.
Failover Behavior Differences Between Static and Dynamic Routing
BGP keepalives trigger automatic route withdrawal within seconds of tunnel failure, whereas static routing leaves stale paths active until manual intervention occurs. Dynamic mechanisms rely on session state monitoring to invalidate prefixes instantly when the underlying IPsec transport collapses. Dynamic BGP data shows dynamic configurations support ECMP aggregation to apply multiple tunnels simultaneously for increased bandwidth. In contrast, static models often limit throughput to a single active tunnel unless complex external scripts manage path selection. A user scenario on AWS re:Post described a Transit Gateway deployment where dynamic routing was necessary for automatically changing routes when the primary S2S VPN failed, a capability not fully supported by static routing without external tools. The trade-off is that debugging these automatic transitions demands deep visibility into BGP timers and peer logs. Operators relying on static entries face prolonged outages because the network lacks intrinsic failure detection logic.
| Failure Event | Static Response | Dynamic BGP Response |
|---|---|---|
| Tunnel Down | Route remains active | Route withdrawn automatically |
| Primary Link Loss | Manual edit required | Immediate failover to secondary |
| Recovery | Manual re-entry needed | Automatic route re-advertisement |
InterLIR analysis indicates that reliance on manual failover scripts introduces unacceptable latency during critical maintenance windows. The absence of automatic path invalidation in static configurations creates a window of vulnerability where traffic blackholes persist undetected. Production networks requiring sub-minute recovery cannot tolerate the operational lag inherent to static route management.
VGW Migration Risks: Mandatory Downtime for Static to Dynamic Conversion
According to VPN Connection Terminated in Virtual Private Gateway (VGW), simultaneous static and dynamic connections are impossible on the same customer gateway, forcing a destructive delete-and-recreate workflow. This architectural constraint mandates a hard cutover where the existing static tunnel must be fully deleted before a new dynamic session can be instantiated. Operators attempting to fix a BGP session not established error often overlook this prerequisite, mistakenly trying to layer protocols rather than replacing the underlying connection object. The Virtual Private Gateway enforces a strict one-connection-per-customer-gateway rule during this transition, creating an unavoidable connectivity.
InterLIR assessment indicates that this limitation transforms what should be a routing protocol upgrade into a scheduled maintenance event requiring explicit downtime approval. Unlike software upgrades, this migration breaks the data plane entirely until the new BGP peering reaches the Established state.
- Delete the existing static VPN connection from the AWS console.
- Create a new customer gateway object specifying the required.
- Provision the new dynamic Site-to-Site VPN linking the updated gateway.
This sequence guarantees traffic loss equal to the provisioning duration plus convergence time. Networks relying on static routes for critical paths face total isolation during this window, as no fallback mechanism exists within the VGW logic. The cost of automation is a brief but absolute service interruption that cannot be mitigated by dual-homing within the same gateway context.
Step-by-Step Migration Guide for AWS Transit Gateway and Virtual Private Gateway
according to Prerequisites for BGP Migration on AWS Transit Gateway and VGW
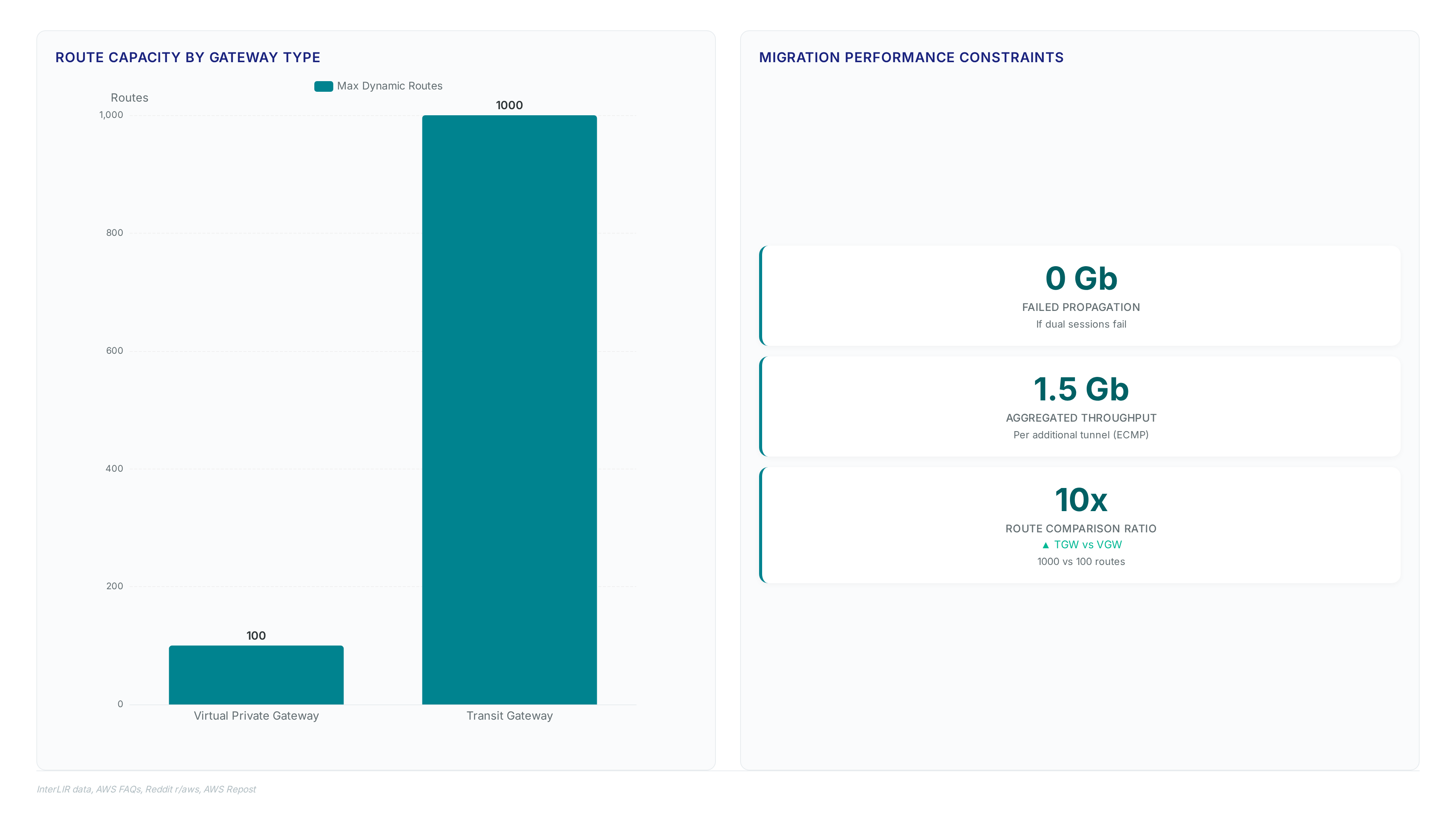
InterLIR, 0 Gb of valid route propagation occurs if the customer gateway fails to terminate both IPsec and BGP sessions simultaneously. This hard constraint demands that devices like Palo Alto Firewall, Cisco ASA, MikroTik RouterOS, pfSense, or OPNsense handle dual-protocol processing without offloading either function to separate hardware modules. Operators must secure a unique BGP Autonomous System Number (ASN) before initiating any configuration changes, as the cloud side rejects peering requests lacking this identifier.
The migration process requires strict adherence to device capability verification:
- Confirm the on-premises unit supports concurrent tunnel encryption and BGP state machine operations.
- Validate that the specific firmware version handles the required number of prefix advertisements.
- Ensure administrative access exists for both the AWS console and the local device.
Legacy hardware often sustains IPsec loads yet collapses under BGP update bursts during convergence events. Packet loss occurs during the initial route exchange phase if CPU resources saturate with encryption tasks. Upgrading firmware to support BGP features can inadvertently alter cryptographic module prioritization, degrading tunnel stability. Successful deployment hinges on verifying that the chosen platform maintains line-rate performance while managing dynamic routing tables.
Executing Zero-as reported by Downtime Parallel Migration for Transit Gateway
Migration Steps for Transit Gateway, running parallel connections enables zero-downtime migration by avoiding the hard cutover required on Virtual Private Gateways. Operators must first document existing static routes and VPC CIDR ranges before initiating the dynamic process. This baseline prevents routing conflicts when both paths temporarily coexist within the Transit Gateway routing domain.
The execution phase requires precise navigation through the AWS console to instantiate the new session without disrupting the legacy tunnel.
- Navigate to the VPC Console and select Site-to-Site VPN connections.
- Click "Create VPN connection" and choose Transit gateway as the target gateway type.
- Select the existing customer gateway object, ensuring it possesses the correct BGP Autonomous System Number (ASN).
- Choose "Dynamic (requires BGP)" for the routing option to enable automatic propagation.
- Download the specific configuration file for your device platform, such as Palo Alto Firewall or Cisco ASA.
Migration Steps for Transit Gateway, selecting the same customer gateway allows the new dynamic session to initialize alongside the static one. The limitation is that this parallel operation functions only on Transit Gateway attachments, not on Virtual Private Gateway endpoints which enforce single-connection limits. InterLIR reports 1.5 Gb of aggregated throughput becomes available once ECMP activates across the dual tunnels.
Traffic validation must occur before deleting the original static entry to confirm route precedence and failover behavior. Skipping verification risks blackholing if the on-premises firewall rejects the new BGP advertisements while the static route remains primary. Network teams should monitor the BGP session state closely to ensure the_fsm reaches Established before shifting production workloads.
Virtual Private Gateway Migration Risks and Mandatory Downtime Windows
The Virtual Private Gateway enforces a single active connection per customer gateway, mandating total service interruption during migration. This architectural constraint prevents the parallel operation required for zero-downtime transitions, forcing operators to delete the existing static tunnel before instantiating the dynamic BGP session. Unlike Transit Gateway environments that support simultaneous connections, this hard limit creates an unavoidable maintenance window where traffic flow drops to 0 Gb until the new session stabilizes. The mechanism relies on strict object uniqueness within the AWS control plane, rejecting any attempt to attach a second VPN connection to the same customer gateway IP address.
Failure to complete step three renders step four impossible, locking the environment in a static-only state until the obsolete object is removed.
Measurable ROI and Operational Best Practices for Enterprise BGP Deployments
Defining Dynamic BGP Route Propagation Limits on AWS VGW and TGW
Transit Gateway handles 1,000 routes while Virtual Private Gateway stops at 100. This tenfold capacity difference dictates architectural choices for enterprises scaling cloud connectivity beyond simple hub-and-spoke topologies. The Virtual Private Gateway imposes a hard ceiling on inbound prefixes that forces aggressive summarization or creates blackholes for granular subnets. In contrast, the Transit Gateway absorbs full table advertisements from on-premises routers without requiring manual aggregation filters. Ignoring these limits causes silent route drops where valid prefixes vanish from the VPC route table. Choosing VGW for cost savings restricts future network segmentation capabilities. A flat network structure might suffice today, but adding micro-segmented zones later triggers a complex re-architecture event. Static configurations often mask this impending ceiling until a merger or acquisition expands the address space unexpectedly. Dynamic propagation solves the scaling issue but introduces dependency on session stability.
| Feature | Virtual Private Gateway | Transit Gateway |
|---|---|---|
| Max Inbound Routes | 100 | 1,000 |
| Max Outbound Routes | 1,000 | 5,000 |
| ECMP Support | No | Yes |
| Migration Path | Destructive cutover | Parallel operation |
Applying ECMP Tunnels to Achieve 5 Gbps Throughput in Site-to-Site VPN
Large Bandwidth Tunnel configurations support 5 Gb throughput per tunnel, shattering the legacy 1.25 Gb ceiling found in standard deployments. This capacity jump relies on terminating Equal-Cost Multi-Path sessions at a Transit Gateway rather than a Virtual Private Gateway. Operators aggregate multiple logical paths to saturate available physical links without purchasing higher-tier single-tunnel services. LexisNexis Risk Solutions resolved performance bottlenecks by shifting traffic to core networks that use this dynamic propagation model. The mechanism distributes frames across active tunnels based on hash algorithms, demanding symmetric path characteristics to prevent out-of-order delivery penalties. Strict hardware synchronization becomes mandatory. Asymmetric latency between aggregated tunnels triggers retransmissions that degrade proven throughput. Most mid-sized enterprises lack the diverse upstream connectivity required to populate multiple high-capacity paths simultaneously. This constraint forces a choice between over-provisioning redundant circuits or accepting lower aggregate bandwidth limits. Network architects must verify that on-premises edge devices can sustain line-rate encryption across all parallel sessions. Failure to balance load correctly results in single-tunnel saturation despite excess capacity.
Pre-Migration Checklist for BGP Session States and ASN Configuration
Validation of 4-byte ASN ranges between 1 and 2,147,483,647 must occur before initiating session handshakes. AWS supported Independent System Number values span this entire integer spectrum, preventing configuration errors on legacy hardware. Operators often overlook that the target device must terminate IPsec encryption and BGP peering processes on the same physical or virtual interface simultaneously. Dynamic routing fails if the customer gateway splits these functions across distinct security zones. InterLIR recommends verifying firmware support for concurrent session handling prior to deleting static routes. A secondary validation step involves confirming the specific gateway type supports multiple active tunnels for redundancy. Static configurations often mask underlying path failures that dynamic protocols immediately expose through state machine transitions. Skipping this audit leads to a failed migration window where neither static nor dynamic paths carry traffic. Network teams should script pre-checks for ASN format compliance to avoid manual typos during high-pressure maintenance windows. Procedural rigor ensures the control plane stabilizes quickly after the data plane cutover occurs.
About
Alexander Timokhin, CEO of InterLIR, brings deep expertise in IT infrastructure and global IP resource management to the complexities of AWS networking. As the leader of a specialized IPv4 marketplace, Timokhin understands that reliable connectivity relies heavily on efficient routing protocols. His daily work involves ensuring clean BGP sessions and secure route objects for clients worldwide, making him uniquely qualified to discuss migrating from static to dynamic BGP routing on AWS Site-to-Site VPNs. At InterLIR, the focus on network availability and transparency directly parallels the need for automatic failover and high-availability in cloud architectures. This article bridges his strategic experience in managing critical network resources with practical guidance for optimizing AWS environments. By using his background in international IT operations, Timokhin provides actionable insights for organizations seeking to enhance their hybrid cloud durability through superior routing strategies.
Conclusion
Scaling beyond the legacy 1.25 Gb ceiling introduces a critical fragility: the transition window where traffic drops to zero until new sessions stabilize. While Bandwidth Tunnel configurations promise 5 Gb throughput, this capability shatters previous limits only if your underlying physical infrastructure supports strict symmetric latency. Asymmetric paths trigger immediate retransmissions that degrade performance faster than single-tunnel saturation ever could. Most organizations fail here not because of AWS limits, but because their on-premises edge devices cannot sustain line-rate encryption across parallel sessions simultaneously. The operational cost of ignoring this is a complex, unstable mesh that requires constant manual intervention rather than delivering promised redundancy.
Adopt high-capacity tunnel modes only after verifying that your upstream connectivity offers diverse, symmetric paths; otherwise, remain on standard configurations until your WAN refresh cycle. Do not attempt this migration during peak business hours, as the stabilization period creates an unacceptable outage risk for real-time applications. You must treat session synchronization as a hard dependency, not an optional optimization.
Start by auditing your current edge device firmware this week to confirm it can terminate IPsec and manage dynamic peering on the same interface without splitting functions across security zones. This specific validation prevents the total routing collapse that occurs when control plane and data plane processes diverge during high-load events.