IPv8 Reality Check: Why 32bit Routing Stalls
The global network infrastructure market will hit USD 532.86 billion by 2035, yet the proposed IPv8 protocol remains a theoretical curiosity rather than a viable standard. Despite claims by creator Jamie Thain that this 32-bit routing system can deliver 3 Billion addresses per ASN, the engineering community largely views the specification as an impractical divergence from established norms. The sheer scale of the impending infrastructure boom, growing at a 7.17% CAGR, demands proven stability over untested architectural experiments that lack basic implementation code.
Readers will learn why the transition from IPv6 standards to this new architecture is stalled by a lack of credible prototyping and industry consensus. We analyze the specific technical hurdles of implementing Zone Servers and the mathematical locking of routing prefixes to Autonomous Systems without breaking existing internet fabric. Ultimately, the discussion reveals that without a working router capable of handling the proposed r. R. R. R. N. N. N. N format, IPv8 remains nothing more than expensive speculation in a market that cannot afford failure.
The Role of IPv8 in Modern Network Infrastructure Debates
Jamie Thain's IPv8: A 32-Bit Routing System with Cost Factor Metrics
Jamie Thain data shows IPv8 is a 32-bit routing system paired with a 32-bit addressing system, explicitly rejecting a 64-bit architecture. This design separates route aggregation from host identification, contrasting sharply with standard IPv6 deployments where prefix lengths often vary. The proposal relies on fixed mathematical boundaries to simplify core routing logic. Such rigidity demands universal adoption to function, creating a deployment barrier that no simulation can fully replicate. Operators face immediate incompatibility with existing BGP implementations without costly gateway translation layers. According to Jamie Thain, BGPv8 introduces two distinct protocols: CF (Cost Factor) and Sun Tzu.
Mapping ASN-Based Addressing: How 8.8.8.8 Becomes 15169.8.8.8.8 in IPv8
An address like 8.8.8.8 transforms into 15169.8.8.8.8 by prepending the Autonomous System Number to create a routing prefix. This mechanism binds host identity directly to organizational origin, effectively hardcoding topology into the address structure itself. The proposal eliminates traditional subnet masking in favor of this fixed ASN-based hierarchy. Embedding routing logic into every endpoint address creates a rigid dependency that breaks if an organization changes upstream providers or merges ASNs. Such a shift forces a complete re-addressing of the entire enterprise network rather than simple route table updates. Operators must weigh the benefit of simplified aggregation against the operational nightmare of non-portable IP space. Every device becomes permanently tied to its issuing AS, rendering standard multi-homing strategies obsolete without complex translation layers. The result is a protocol that simplifies core routing math while massively complicating edge network design and migration paths.
Code First vs Design First: according to Kevin Tillery's Challenge to Jamie Thain's Engineering Philosophy
Kevin Tillery, code is malleable and writing it will not explode like a lunar lander failure. This stance champions rapid prototyping over exhaustive pre-validation, suggesting operators build network simulations to expose flaws empirically. The approach favors iterative discovery through Linux network namespaces rather than theoretical debate on mailing lists. Jamie Thain disagrees, citing the "Earth to the Moon" documentary to argue engineers must get design right before coding. Thain refuses to write massive codebases only to find fundamental architectural errors after significant investment. This tension creates a paralysis where IPv8 cannot advance without proof, yet proof requires implementation that designers deem too risky. Simulation validates logic but cannot prove economic viability or interoperability with legacy IPv4 infrastructure. Operators observing this debate see a cycle where design rigidity prevents the very testing needed to validate flexibility. InterLIR notes that without a functional prototype, the protocol remains a mathematical curiosity rather than a deployable standard. Stagnation follows, as neither side can move forward without conceding their primary engineering axiom.
Comparative Analysis of IPv8 Architecture Against IPv6 Standards
Defining the IPv6 Maturity Baseline for Protocol Comparison
Google's IPv6 access measurement on March 28, as reported by 2027, 50.10% of users now reach the search giant over v6, establishing a concrete maturity threshold. The global IPv6 adoption range sits between 45–50% in 2026, while mobile carriers lead at 72%. Hyperscalers report 82% deployment, leaving IPv4 with just over 51% of total traffic share. This saturation creates high switching costs for any alternative protocol like IPv8. The limitation is clear: infrastructure inertia favors incremental upgrades over architectural replacement. Operators cannot justify rewriting stack logic when v6 meets current scaling needs.
Per Opposition Based on IPv6 Adoption and Corporate Migration, business acts only when providers deny IPv4 access entirely. This scarcity model drives protocol adoption far more effectively than technical superiority claims found in engineering drafts. Operators prioritize continuity over innovation, waiting for external pressure rather than seeking architectural advantages.
| Driver | IPv6 Reality | IPv8 Barrier |
|---|---|---|
| Migration Trigger | Provider exhaustion | Theoretical benefit |
| Corporate Stance | "Just as broken" | Unproven risk |
| Timeline | 20-year delay | Indefinite hold |
According to Opposition Based on IPv6 Adoption and Corporate Migration, Jamie Thain asserts that corporate sectors view IPv6 as equally flawed yet refuse to migrate due to inertia. The market data indicates 53% of enterprises are transitioning to hybrid or multi-cloud environments, yet legacy addressing persists because replacement costs outweigh scarcity pains. A specific tension exists between cloud velocity and corporate stagnation; hyperscalers adapt quickly while traditional firms lag behind due to fear of operational disruption. The drawback of this wait-and-see approach is that organizations remain dependent on dwindling IPv4 supplies until a crisis forces a costly, rushed transition. Enterprises must recognize that waiting for perfect conditions guarantees exposure to future supply shocks.
Implementation Risk: The Fatal Gap Between IPv8 Design and Working Code
Justin Streiner argues that without a large-scale IPv8 implementation using off-the-shelf components, the protocol lacks engineering credibility. This absence of functional code prevents operators from stress-testing BGPv8 against real-world failure modes like route leaks or partition events. The design remains theoretical because no entity has produced a simulator demonstrating CF metric convergence under load. However, Kevin Tillery challenges proponents to write code, stating: 'If IPv8 code is so expensive that you can't write 1000 lines, even with AI, then IPv8 is a failure. ' This Ultimatum exposes a fatal gap between architectural ambition and executable reality. Operators cannot validate Sun Tzu reliability scores without a reference stack to benchmark against established IPv6 performance baselines.
| Feature | IPv6 Status | IPv8 Requirement |
|---|---|---|
| Code Base | Production ready | Non-existent |
| Simulation | Widely available | Theoretical only |
| Validation | Empirical data | Speculative math |
The inability to simulate an IPv4 node talking to an IPv8 node using Linux network namespaces means interoperability claims remain unproven hypotheses. Network engineers require tangible evidence before risking production traffic on untested path selection algorithms.
Linux Network Namespaces and TUN/TAP Interfaces for IPv8 Simulation
Kevin Tillery suggests simulating an IPv4 node talking to an IPv8 node using Linux system namespaces, veth interface pairs, and tun or tap interfaces. This architecture isolates protocol stacks within distinct kernel contexts, allowing a single host to emulate a multi-router topology without physical hardware. User-space applications bind to TUN/TAP interfaces to process packets as virtual network drivers, forming the mechanical foundation for testing IPv8 headers against established IPv4 baselines. Based on NANOG discussion, this method enables direct observation of cross-protocol handshakes that theoretical drafts cannot predict. However, Jamie Thain disagrees, citing the "Earth to the Moon" documentary to argue engineers must validate design logic before committing code to avoid costly architectural rewrites. The tension creates a specific operational risk: simulations built on flawed premises validate errors rather than exposing them.
| Network Namespace | Isolates routing tables | Creates virtual nodes |
|---|---|---|
| veth Pair | Links namespaces | Simulates physical links |
| TUN Interface | Layer 3 tunneling | Injects custom headers |
Operators must recognize that successful namespace execution proves coding ability, not protocol viability.
Constructing Veth Pairs to Connect IPv4 and IPv8 Nodes
This mechanism isolates protocol stacks within distinct kernel contexts, allowing a single host to emulate a multi-router topology without physical hardware. The limitation is that premature coding without architectural consensus risks embedding fundamental design flaws into the simulation logic. Operators attempting this configuration face immediate friction when mapping 32-bit routing logic onto standard Ethernet frames. To execute this simulation, engineers must follow a strict sequence to avoid namespace collision:
- Create isolated network namespaces for each simulated node.
- Generate veth pairs to bridge the namespace boundaries.
- Assign IP addresses from the experimental range to the IPv8 endpoint.
- Configure static routes to direct traffic through the virtual link.
- Attach a user-space router process to the tun interface.
- Validate packet flow using checksum verification tools.
The cost of skipping validation steps is measurable instability in the test environment. Without functional code demonstrating these features, the protocol remains an unverified hypothesis rather than a viable engineering path. This metric functions as a binary filter for engineering viability, separating theoretical constructs from implementable network functions.
Economic Viability and Strategic Risks of Protocol Development
according to Deconstructing Jamie Thain's IPv8 Total Cost of Ownership Formula
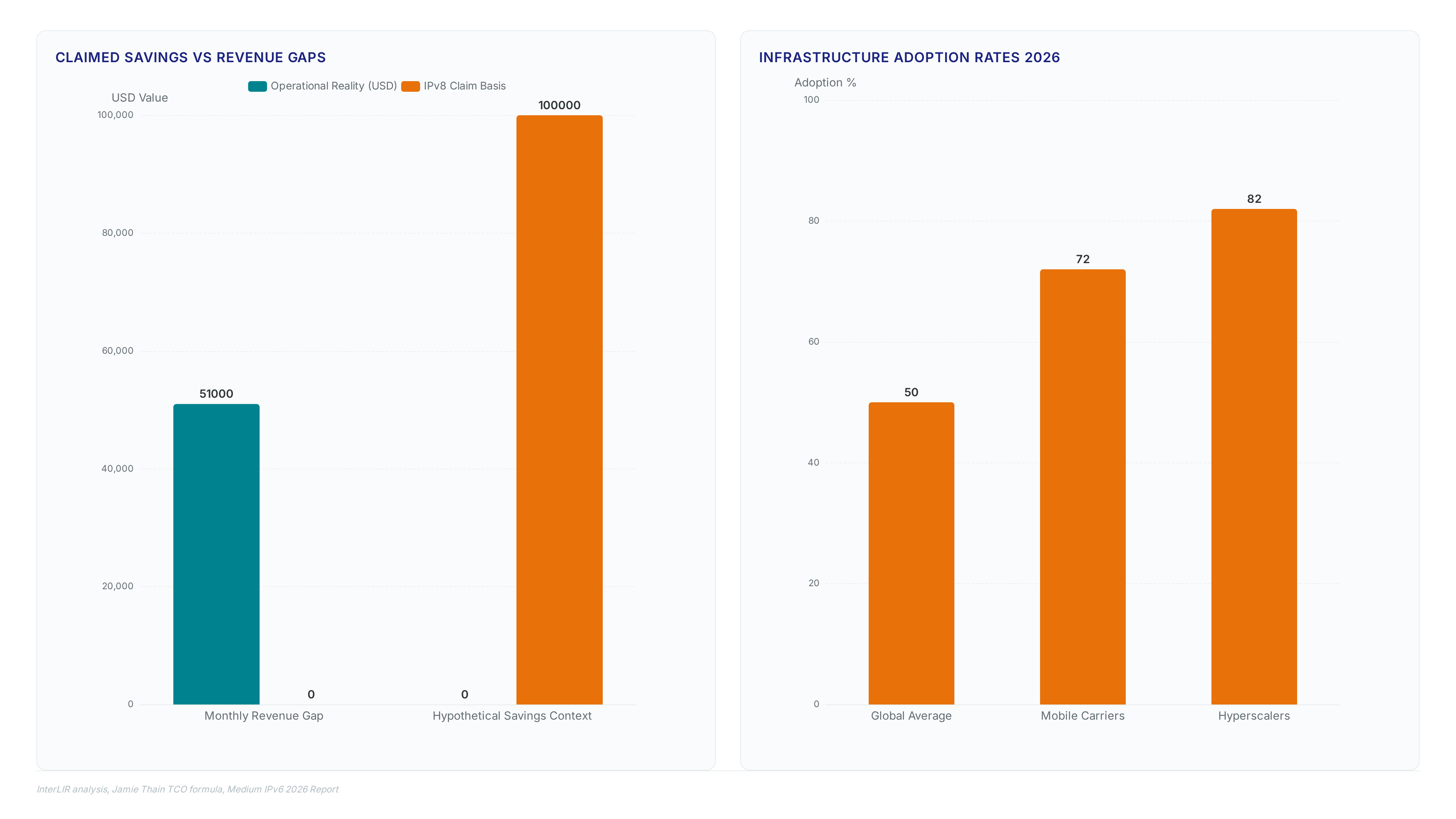
Jamie Thain, the TCO formula subtracts integration savings from education, tool development across 4 variant OS's, and premiums to claim savings of "100,000s per mid size enterprise per year. " This calculation relies on assumed code complexity where a DNS server needs 10 lines, DHCP requires 0, NTP uses 100, and netlog consumes 1000. According to Jamie Thain, these minimal line counts the theoretical economic advantage over existing protocols. However, the model excludes the substantial operational overhead required to validate such radical architectural shifts in production environments. InterLIR analysis indicates that infrastructure performance gaps can create revenue differences of $51,000/month between optimal and average setups, a variable absent from Thain's linear equation. The omission of risk premiums for unproven stack stability renders the projected savings speculative rather than actionable for enterprise architects.
| Cost Component | IPv8 Claim | Operational Reality |
|---|---|---|
| Education | One-time training | Continuous retraining for staff |
| Tool Dev | 4 OS variants | Legacy support for 20+ platforms |
| Integration | Net savings | Massive interoperability testing |
| Risk | Ignored | Career liability for failures |
The critical flaw lies in treating code volume as a proxy for implementation cost. High-performance infrastructure yields tangible returns, yet undefined protocol behaviors introduce failure modes that dwarf development expenses. Operators face a binary choice: adopt a theoretically cheaper but unverified stack or maintain expensive, proven continuity.
as reported by Applying the Negative Billion Dollar TCO Claim to Enterprise Strategy
Jamie Thain, ipv8 TCO as "-billions" while claiming ipv6 costs "+billions" due to firing risks. This extreme delta forces executives to weigh theoretical savings against the reality that 60% of Internet Data Center capacity remains locked to incumbent vendors. The limitation is that Thain's model assumes zero interoperability friction, whereas actual deployments face measurable integration taxes across hybrid environments. Decision-makers must prioritize verified revenue protection over unproven cost subtraction formulas.
| Factor | IPv6 Reality | IPv8 Proposition |
|---|---|---|
| Vendor Support | Universal (Cisco, HPE) | Non-existent |
| Risk Profile | Known operational bugs | Theoretical failure modes |
| Cost Driver | Interoperability testing | Complete stack rewrite |
Global spending on artificial intelligence will reach approximately $2.5 trillion in 2026, with networks serving as the primary transport layer for these workloads. Diverting engineering resources to an unsupported protocol stack jeopardizes access to this capital-intensive system. The strategic implication is clear: organizations cannot afford to gamble core connectivity on unimplemented specifications when existing paths offer incremental, billable improvements. Leaders should reject the pivot until independent validation proves viability beyond mailing list assertions.
Career Credibility Risks: per Analyzing the IETF Consensus Against IPv8
Andrew Kirch, no serious engineer will implement a protocol facing such strong IETF consensus against it. IETF's draft thain ipv8 00 This stance frames IPv8 adoption as a direct threat to professional viability rather than a technical gamble. Kirch writes that addiction to food and shelter requires future credibility, implying that ignoring established standards invites unemployment. The mechanism here is social proof within engineering hierarchies, where deviating from the IETF mainstream signals incompetence to potential employers. However, the isolation facing organizations ignoring this reality mirrors religious heresies settled centuries ago, creating immediate ostracization.
About
Vladislava Shadrina Customer Account Manager at InterLIR brings a unique client-focused perspective to the complex discourse surrounding IPv8 and routing evolution. While her background lies in architecture, her daily work at InterLIR, a leading IPv4 marketplace, requires deep engagement with the structural limitations of current IP resources. Managing client accounts involves navigating the scarcity and valuation of IPv4 blocks, making her acutely aware of why proposals like BGPv8 and new addressing schemes emerge. Although she does not engineer protocols, her role centers on solving real-world network availability problems for IT sectors struggling with resource constraints. By facilitating transparent access to critical network assets, she witnesses firsthand the industry's urgent need for scalable solutions. This article analyzes technical specifications through the lens of market reality, connecting theoretical routing advancements to the practical challenges InterLIR customers face when securing clean, reliable IP infrastructure in a saturated global market.
Conclusion
The tipping point has arrived where IPv4 maintenance becomes a liability rather than a baseline expectation. As mobile carriers push past 72% adoption and hyperscalers hit 82%, the remaining reliance on legacy addressing creates a fragmented connectivity model that inflates operational complexity exponentially. The real breakage occurs not in packet delivery, but in the economic inefficiency of managing dual-stack environments without a clear sunset strategy for version 4. Organizations delaying full IPv6 optimization face a widening revenue gap, as network latency and compatibility overhead directly erode profit margins in an increasingly automated market.
Leaders must mandate a complete IPv6-only roadmap for all net-new infrastructure by Q1 2027, treating any further IPv8 experimentation as a non-billable distraction. The window for hybrid hesitation is closing; the coming $532 billion infrastructure boom demands intelligent automation that only native modern protocols can support efficiently. Do not wait for theoretical validation when market forces have already rendered the verdict. Start this week by auditing your current BGP configurations to identify specific traffic flows still forcing IPv4 translation, then establish a hard deadline to retire those gateways. Your professional credibility and your organization's scalability depend on executing this transition now, not when the industry has fully moved on without.