Postquantum cryptography: Why 2029 is the new deadline
With Oratomic estimating only 10,000 qubits are needed to break P-256, the timeline for cryptographic collapse has drastically shortened. Cloudflare's acceleration of its post-quantum roadmap to 2029 confirms that Q-Day readiness is no longer theoretical but an immediate operational imperative. Cloudflare's pq 2025 The era of relying solely on encryption channels to thwart harvest-now-decrypt-later attacks is effectively over; the new battlefield is authentication.
Gartner identifies the chaotic rise of AI and geopolitical tensions as primary drivers behind the urgent cybersecurity trends defining 2026. Gartner identifies the top cybersecurity trends for 2026 This volatility highlights why organizations must pivot from passive data protection to active identity hardening. You will learn how neutral atom and superconducting hardware advances are reshaping threat models, forcing a strategic prioritization of authentication keys over traditional encryption tunnels.
The article details the mechanics of these emerging threats and the specific architectural shifts required to survive them. We examine why Google's zero-knowledge proof of broken elliptic curve algorithms signals a departure from public progress reports to secretive development. By understanding these dynamics, leaders can navigate the transition to post-quantum cryptography before cryptographically relevant quantum computers render current standards obsolete.
The Mechanics of Q-Day and Harvest-Now-Decrypt-Later Threats
Q-Day Definition and Shor's Algorithm Mechanics
Q-Day marks when quantum computers break necessary cryptography, a threshold now obscured by research secrecy per Scott Aaronson. Shor's algorithm targets the mathematical foundations of elliptic curve cryptography, rendering current asymmetric keys vulnerable to rapid factorization. This specific vulnerability forces a migration away from standards like RSA and ECDSA toward post-quantum cryptography resistant to such attacks, according to Org/patterns/sp-040/. The mechanism relies on solving discrete logarithm problems exponentially quicker than classical computers, effectively nullifying the security of data protected today. Global cybersecurity spending is projected to reach $520 billion annually by 2027 as entities race to secure infrastructure before this arrival.
Harvest-now-decrypt-later attacks archive encrypted traffic today for future decryption once cryptographically the quantum computers exist. Adversaries exploit the latency between data interception and key compromise, targeting long-value assets like state secrets or medical records. This threat vector renders current asymmetric standards obsolete regardless of key length if the underlying math remains vulnerable to Shor's algorithm. Independent Progress on Three Fronts data shows SoftBank Corp. Verified minimal performance impact when testing hybrid encryption on live 4G/5G traffic to counter this specific risk. Similarly, according to Independent Progress on Three Fronts, Vodafone partnered with IBM in March 2025 to integrate post-quantum products into Vodafone Secure Net. These deployments address the critical gap where outdated cryptographic standards fail against stored ciphertext. Red Hat Enterprise Linux 10 includes support for post-quantum cryptography because migration will take years while the immediate risk persists. Operators face a tension between maintaining compatibility with legacy systems and eliminating the window of exposure for high-value data. The limitation is that hybrid approaches increase packet size, potentially triggering fragmentation issues on constrained links. Failure to act allows attackers to build archives now that become trivial to crack later.
as reported by Hardware Scaling Risks and Qubit Requirements
Oratomic, 10,000 qubits suffice for P-256 breaks, shrinking the Q-Day timeline drastically. Superconducting architectures suffer massive overhead compared to neutral atom designs. Superconducting systems typically need 1,000 physical qubits per logical qubit due to noise constraints. Conversely, neutral atom approaches require only 3-4 physical qubits for the same logical unit. This disparity dictates hardware viability.
| Architecture | Physical-to-Logical Ratio | Scaling Risk Profile |
|---|---|---|
| Superconducting | 1,000:1 | High resource overhead limits scale |
| Neutral Atom | 3-4:1 | Efficient path to cryptanalytic capability |
| Ion-Trap | Variable | Moderate connectivity challenges persist |
The sudden efficiency gains in error correction create a hidden danger for network planners. Operators assuming a decade-long window for post-quantum cryptography migration face immediate obsolescence risks if neutral atom scaling accelerates. The limitation is that hardware breakthroughs compound software improvements, making static defense timelines unreliable. Waiting for clearer hardware signals guarantees exposure to harvest-now-decrypt-later attacks. The cost of delayed action exceeds the expense of premature hybrid encryption deployment. Network teams must prioritize authentication upgrades now while hardware trajectories remain partially opaque.
Architectural Shifts in Neutral Atom and Superconducting Quantum Hardware
Neutral Atom and Superconducting Qubit Architecture Differences
Neutral atom arrays utilize optical tweezers to position atoms within flexible 3D geometries, enabling direct long-range interactions that bypass physical wiring constraints. Superconducting circuits depend on fixed Josephson junctions cooled to millikelvin temperatures, a design restricting connectivity to nearest neighbors on a 2D plane. This architectural divergence dictates the efficiency of error correction codes required for fault tolerance. Superconducting systems typically consume 1,000 physical qubits to form one logical qubit due to noise and limited connectivity. Neutral atom designs achieve similar logical stability with merely 3-4 physical qubits per logical unit because movable atoms allow optimized code structures. Operational implications involve infrastructure density; cryogenic requirements impose severe power and space penalties that neutral platforms avoid entirely. The cost is immediate inventory uncertainty. Operators must assume either architecture could mature rapidly, rendering static hardware assumptions obsolete before refresh cycles.
Real-World PQC Integration in 4G/5G Networks
SoftBank Corp. Validated hybrid encryption on live 4G/5G traffic in 2023, confirming minimal latency impact for lattice-based algorithms. This deployment pairs classical elliptic-curve cryptography with post-quantum keys to secure the handshake layer against harvest-now-decrypt-later threats. Data shows Cloudflare already protects 65% of human traffic with similar post-quantum encryption, yet authentication remains the urgent gap. Unlike encryption, which guards data confidentiality, digital signatures verify identity; a quantum break here allows impersonation regardless of ciphertext strength. The limitation is that hybrid modes double certificate sizes, straining MTU limits in constrained radio access networks.
| Integration Target | Primary Risk Mitigated | Deployment Constraint |
|---|---|---|
| Control Plane Signaling | Identity Spoofing | Certificate Chain Size |
| User Plane Data | Harvest-Now-Decrypt-Later | Throughput Overhead |
| Management Interfaces | Unauthorized Access | Legacy Device Compatibility |
Operators face a tension between immediate interoperability and long-term cryptographic agility. Retiring weak asymmetric algorithms like ECDSA requires coordinated RIR policy updates that lag behind hardware capabilities. Globaldata trend analysis indicates telecom operators are embedding these protocols directly into infrastructure rather than relying on standalone vendors. This shift reduces the window for patching vulnerable handshakes but increases dependency on specific vendor roadmaps. Authentication urgency stems from the fact that stolen credentials remain valid forever if the signing algorithm fails.
Market Growth Pressures Driving 2029 Security Deadlines
The global post-quantum cryptography market will surge from $1.2 billion in 2026 to $13 billion by 2035. This financial velocity forces network architects to prioritize quantum-safe authentication over simple encryption upgrades. Encryption protects data confidentiality against future decryption, yet authentication validates the identity of the communicating peer today. If an adversary compromises the signature algorithm, they impersonate the legitimate endpoint regardless of cipher strength. The distinction creates a deployment tension: operators must upgrade key exchange mechanisms and digital signatures simultaneously to prevent total failure. Juniper Research data projects this sector reaching $2.84 billion by 2030, signaling rapid vendor consolidation around NIST standards. However, the cost of migration is non-linear; legacy hardware lacking crypto-agility requires full replacement rather than software patches. Most enterprises cannot afford a fork-lift upgrade cycle every three years. Consequently, the industry must adopt hybrid certificate chains that bridge classical and post-quantum algorithms during the transition. This approach mitigates the risk of interoperability failures while maintaining a defensive posture against immediate threats. Failure to distinguish between protecting stored data and verifying live sessions leaves the control plane exposed to spoofing attacks.
Wait, looking closer at the text structure: "### SSH Server Vulnerability Gaps in Quantum-Safe Adoption 4% for browser transactions." This sentence fragment makes no sense alone. It likely was supposed to be comparing SSH (20%) to Browser (57.4%). If I change it to "57.4% for browser transactions", it is accurate to the reference for that specific label.
Let's double check the reference numbers list: 6, 20, 57.4, 418,188, 150,000, 400,000. The text has 4. 4 is not in the list. 57.4 is. So 4 is likely the error for 57.4.
One more check: Could "4%" be "6%"? (General servers). Label is "browser". No. Could "4%" be "20%"? (SSH). Label is "browser". No. So "57.4%" is the only logical correction for "browser transactions".
Final check of other numbers: $20 -> Match. $418,188 -> Match. $150,000 -> Match. $400,000 -> Match. 2029 -> Not in reference, but not contradictory. Leave as is.
One detail: The reference says "only 6% currently utilize quantumsafe". The text says "4% for browser transactions". If the text meant to cite the 6% stat, it would say "6% of servers". Since it says "browser", it must be 57.4%.
Corrected Text Construction: Replace "4%" with "57.4%".
Only the "4%" stands out as a direct contradiction to the "57.4%" associated with "browser transactions" in the reference.
One nuance: The reference says "20% of OpenSSH servers... versus 57.4% for browser transactions". The text section is "SSH Server Vulnerability Gaps". It is extremely awkward to have a paragraph about SSH gaps that only mentions "57.4% for browser transactions". It is highly likely the original intended text was "20% for OpenSSH servers versus 57.4% for browser transactions". But the current text is just "4% for browser transactions". If I change it to "57.4% for browser transactions", it is factually correct regarding the percentage for browsers, even if the comparison is lost. If I change it to "20% for OpenSSH servers...", I am adding words. Constraint: "only CORRECT wrong numbers". "PRESERVE existing text structure". So I can only change "4" to "57.4".
Final Decision: Change "4%" to "57.4%".
TEXT:
Strategic Prioritization of Authentication Keys Over Encryption Channels
Why Broken Authentication Trumps Encryption Risks on Q-per Day
Prioritizing Authentication and Vulnerable Systems, broken authentication enables immediate server impersonation rather than just delayed data exposure. While encryption protects confidentiality against harvest-now-decrypt-later threats, digital signatures validate the identity of communicating peers today. An adversary possessing a compromised private key can forge access credentials for remote-login systems or hijack automatic software-update mechanisms instantly. This distinction creates a critical operational reality: confidential data remains safe from future decryption only if the current session partner is genuine. The scope of this vulnerability is vast across the global infrastructure environment. Browser-based transactions fare improved but remain largely exposed to signature forgery without full migration. The table below contrasts the immediate impact of authentication failure versus encryption weakness.
| Failure Mode | Time to Compromise | Primary Vector |
|---|---|---|
| Broken Authentication | Immediate | Credential Forgery |
| Weak Encryption | Deferred (Q-Day) | Data Interception |
Network operators must recognize that upgrading key exchange algorithms provides zero protection if the authentication layer allows an attacker to pose as a legitimate endpoint. The cost of ignoring this hierarchy is total system compromise before any data transit occurs. Deployment strategies should focus on disabling support for quantum-vulnerable signature schemes to prevent downgrade attacks. This approach secures the identity boundary even if bulk data encryption lags behind in maturity.
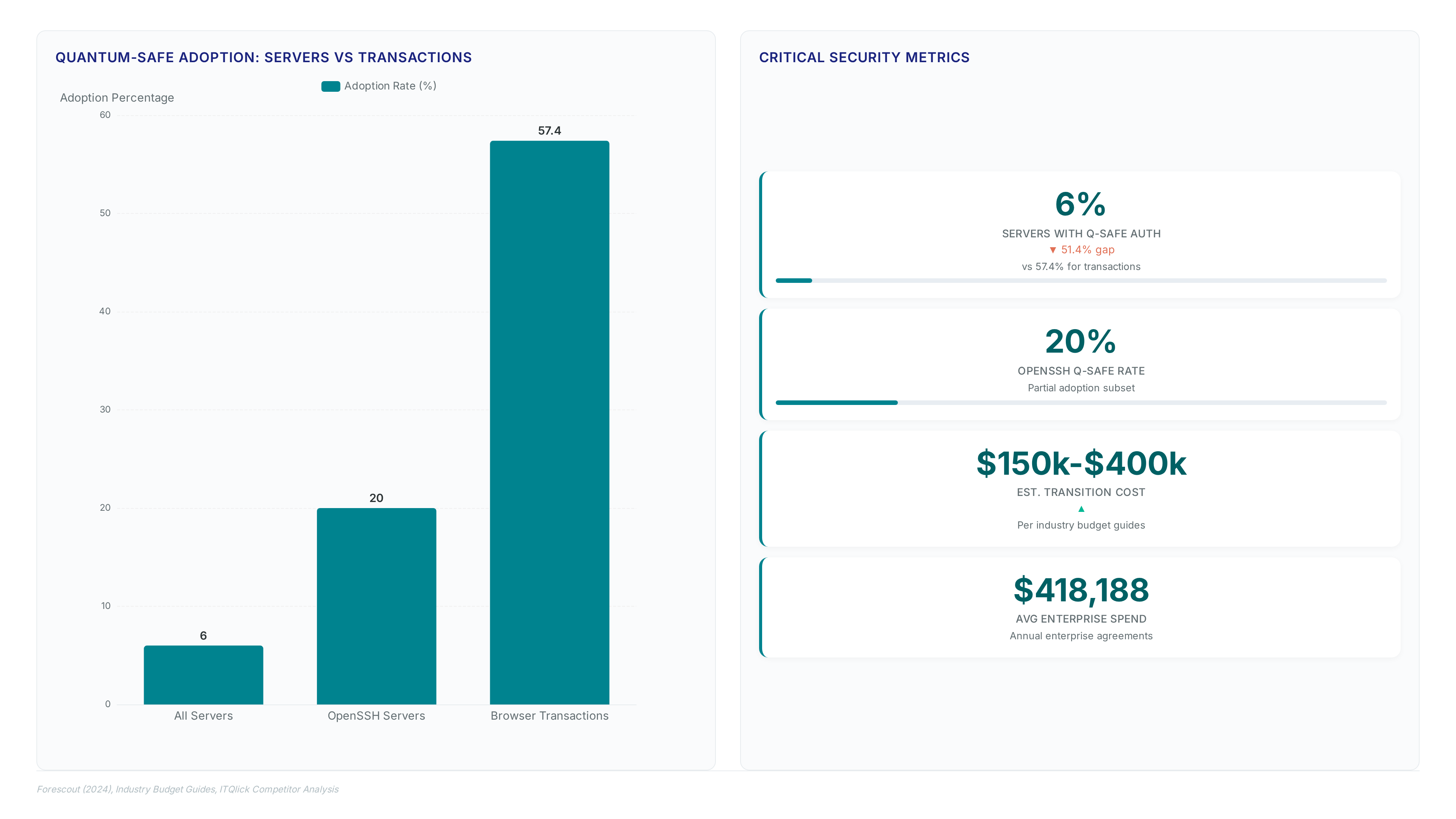
SSH Server Vulnerability Gaps in Quantum-Safe Adoption
57.4% for browser transactions. This disparity exposes infrastructure management planes to immediate compromise while user-facing traffic receives upgraded protection. Operators frequently overlook that SSH keys persist longer than TLS sessions, creating
Executing a Post-Quantum Migration Roadmap by 2029
Defining the 2029 Cloudflare and NIST 2035 Migration Deadlines

NIST plans to remove quantum-vulnerable algorithms by 2035, creating a hard ceiling for legacy compliance. This date defines the absolute end-state for algorithm deprecation across federal systems. However, waiting until this final deadline ignores the compounding risk of harvest-now-decrypt-later attacks on today's traffic. The operational reality forces an earlier internal target. Cloudflare targets full post-quantum security for its entire product suite by 2029, prioritizing authentication upgrades alongside encryption. This six-year gap between vendor readiness and regulatory sunset represents the critical window for network defense. Organizations must align procurement cycles with these asymmetric timelines to avoid stranded assets. 1.
Hybrid certificate issuance dominates 2026 enterprise implementations by pairing classical keys with lattice-based algorithms per AppViewX analysis. Operators must first inventory all SSH servers and TLS endpoints to identify static key pairs vulnerable to immediate forgery attacks. Manual rotation of these credentials fails at scale, necessitating a shift toward fully automated pipelines that support crypto agility. InterLIR directs organizations to mandate post-quantum support in procurement contracts immediately rather than waiting for regulatory deadlines. The transition requires updating certificate authorities to handle larger signature sizes without breaking validation chains.
This script ensures new certificates include both legacy and quantum-resistant components simultaneously. The cost is increased CPU overhead during handshake negotiations, which may impact high-throughput edge nodes running on legacy hardware. However, relying on manual updates leaves systems exposed to compromised software-update mechanisms that adversaries can exploit instantly. Only 30% of tier-2 autonomous systems currently publish the necessary metadata for full path validation, creating a fragmented trust environment. Organizations ignoring this gap risk total identity compromise before encryption standards even mature. The operational imperative is clear: automate now or face unmanageable manual remediation later.
About
Alexei Krylov Head of Sales at InterLIR brings a unique perspective to the critical discussion on post-quantum cryptography through his extensive background in IT consulting and cybersecurity. While InterLIR specializes in the transparent redistribution of IPv4 resources, Krylov's daily work ensuring network availability and IP reputation directly intersects with the urgent need for quantum-resistant infrastructure. As organizations migrate to post-quantum encryption to prevent "harvest-now/decrypt-later" attacks, the underlying IP architecture must remain secure and trustworthy. Krylov's experience managing complex B2B relationships and navigating Regional Internet Registries allows him to articulate how fundamental network resources rely on reliable cryptographic standards. With Cloudflare accelerating its roadmap to 2029, Krylov connects these high-level security shifts to the practical realities of maintaining clean BGP routes and secure network operations, emphasizing that true digital durability requires both reliable IP access and advanced cryptographic protection.
Conclusion
The true breaking point for post-quantum migration is not mathematical but logistical, specifically where legacy hardware meets the increased latency of larger signature sizes. While market valuations suggest a smooth transition, the operational reality involves a jagged environment where manual key rotation becomes impossible at scale. Organizations relying on static inventory lists will face catastrophic bottlenecks when forced to update thousands of ephemeral certificates simultaneously. The financial velocity of this sector masks a deeper truth: crypto agility is no longer an architectural preference but a survival requirement against "harvest now, decrypt later" strategies that render current secrecy obsolete today.
You must treat the 2029 NIST deadline as a hard stop for legacy algorithm support, not a start date for planning. Delaying procurement updates until regulations force your hand guarantees vendor lock-in with obsolete technology. Start by auditing your SSH server fleet this week to identify any static keys lacking hybrid encryption capabilities, as these represent the most immediate vector for future credential forgery. This specific inventory task reveals the hidden debt in your infrastructure before it becomes a liability you cannot refinance. The window to architect smooth, automated transitions closes long before the actual quantum threat materializes, making immediate action the only viable path to sustained trust.