SCION routing fixes fragile global internet paths
Over 80 participants attended a dedicated RIPE 81 session to discuss integrating SCION with Regional Internet Registries, signaling a shift away from fragile legacy routing. Digital sovereignty demands an architecture where nations and banks control their own data paths rather than relying on the opportunistic security of the current global grid. Readers will discover how PKI certificates replace vague peering agreements with mathematically verifiable bandwidth contracts, ensuring equity among participants. We examine why Switzerland has already deployed a production BGP-free network for its financial and government sectors, rejecting the instability that plagues the wider internet. The discussion extends to how low-latency trading firms utilize these guaranteed paths to eliminate the jitter that costs millions in missed arbitrage opportunities.
While the broader Software-Defined Networking market expands rapidly, true durability requires more than just decoupling control planes; it demands a fundamental rewrite of routing trust. Unlike the current system where security is an afterthought, this model bakes verification into every packet hop. As geopolitical tensions rise, the ability to isolate national traffic from foreign interference transforms network routing from a utility into a strategic asset.
The Role of SCION in Restoring Digital Sovereignty to Network Routing
SCION Architecture and Trust Domain Hierarchy
ETH Zurich data shows SCION emerged in 2011 to replace BGP's insecure flat model with a hierarchical trust structure. The architecture divides Autonomous Domains into Isolation Domains that enforce explicit cryptographic boundaries. According to IEEE Security & Privacy, this hierarchy replaces implicit peer acceptance with verified certificate chains. According to Adrian Perrig, the legacy internet resembles a "boat full of holes" due to missing path validation. Operators gain sovereignty by defining exactly which upstream providers carry their traffic within each domain.
Every packet carries proof of authorized paths through the network core. This mechanism prevents unauthorized route injection at the source rather than filtering it at the edge. Deploying this model requires replacing or overlaying existing BGP infrastructure with PKI-based agents. Operational complexity rises during migration because legacy routers lack native support for path-segment verification.
Coordination of trust anchors across organizational boundaries proves difficult for most operators. Widespread adoption remains necessary to realize full path diversity benefits. Digital sovereignty requires controlling these trust roots rather than inheriting global defaults. Network teams must weigh the certainty of isolated domains against the ubiquity of the current fabric.
Swiss Federal Deployment and BGP-Free Production Networks
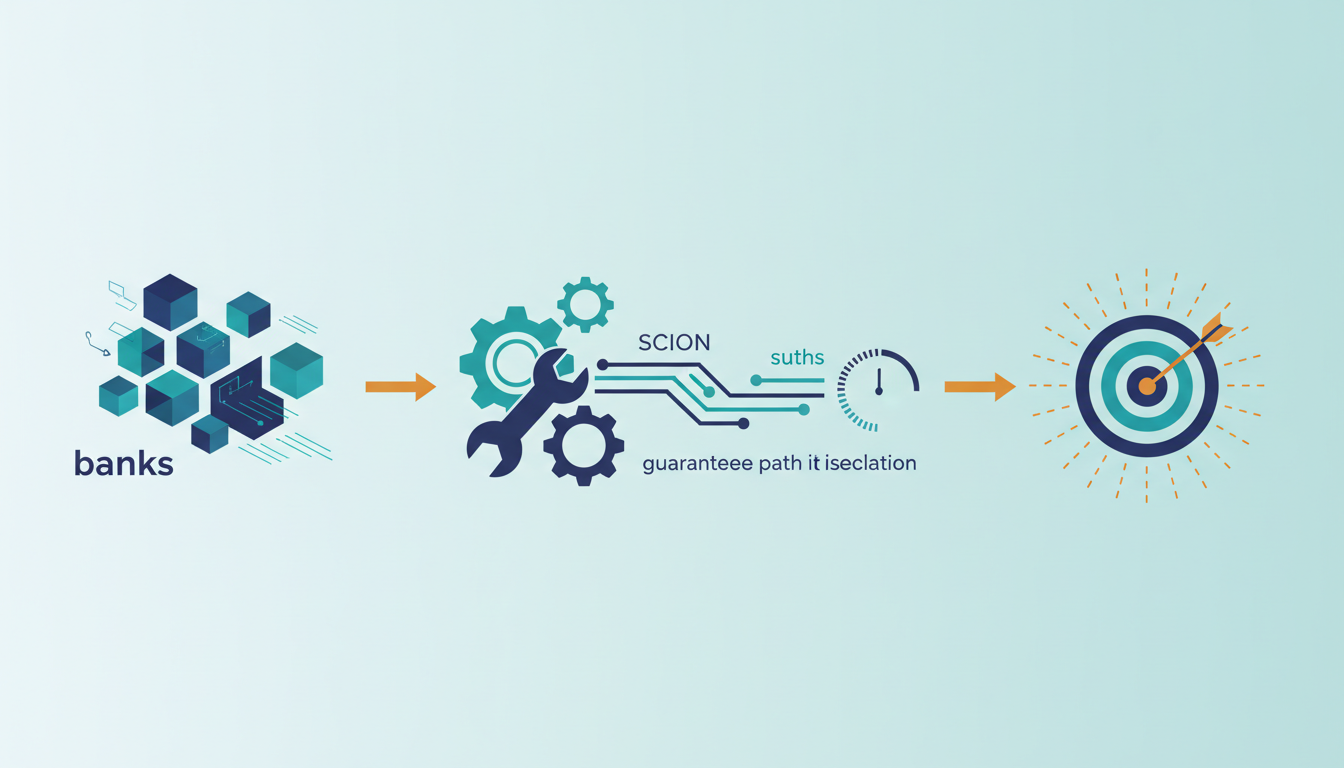
Swiss Federal Council data from 30 October 2025 confirms SCION now carries production traffic for banks and the federal government without BGP. This BGP-free production network spans multiple ISPs across Europe and Asia to validate digital sovereignty claims with operational traffic. Unlike native routing where path selection relies on implicit trust, this overlay network enforces explicit cryptographic authorization for every packet flow. As reported by APNIC blog, over 70,000 different networks currently connect via BGP, creating a massive attack surface that SCION avoids by design. APNIC's future internet at terabit speeds scion in p4 The mechanism replaces dynamic peer updates with static, pre-validated path segments that guarantee latency and prevent route hijacking at the source.
Coordinating certificate policies across independent providers creates a logistical hurdle slowing broader adoption beyond niche critical infrastructure. Network operators must weigh the benefit of deterministic performance against the operational overhead of maintaining separate PKI hierarchies for each trust domain. Financial institutions can bypass global routing volatility for domestic and regional transfers using this existing network. Reliance on a small consortium of participating ISPs introduces a different form of concentration risk that demands diverse physical interconnection points. True durability requires more than just protocol substitution; it necessitates redundant physical fiber routes that do not share conduit with legacy internetExchange points. Operators observing this deployment see a clear trade-off between universal connectivity and guaranteed service levels for high-value transactions. The Swiss model demonstrates that national security interests can drive architectural shifts when commercial incentives alone fail to address systemic routing vulnerabilities.
Inside SCION: How PKI Certificates and Bandwidth Contracts Enable Deterministic Routing
PKI Certificates and Bandwidth Contracts in SCION Routing
Public Key Infrastructure certificates bind bandwidth contracts to cryptographic identities inside SCION. Domains sign explicit capacity agreements rather than relying on the implicit best-effort model found in BGP. This coordination model imposes price adjustments and certificate validation to ensure equity between communicating parties. Operators manage these certificates centrally within each Trust Domain to maintain valid path segments. Such verification enables Path-Aware Networking.
Bilateral contract negotiation creates friction absent in default-accept architectures. Most operators avoid complex pricing logic, preferring simple peering over dynamic rate adjustments. High-value links justify this administrative burden only when latency certainty matters. InterLIR guidance indicates that successful deployments isolate certificate management from daily forwarding operations to reduce human error. Bandwidth availability becomes mathematically provable before packet transmission begins. Failure to renew a specific certificate instantly invalidates associated paths, preventing unauthorized usage but risking outages if automation lags. Deterministic performance relies entirely on strict adherence to cryptographic validity windows.
Deploying SCION as a BGP-per Independent Overlay with Galvanic Isolation
Netherlands deployment, a galvanically isolated connection operating separately from the BGP-controlled internet. This implementation proves SCION functions as a sovereign overlay without relying on unstable external routing fabrics. Operators install the free and open-source project atop existing IP or MPLS forwarding layers to bypass legacy constraints.
- Configure border routers to exchange Path-Aware Networking segments instead of standard reachability advertisements.
- Embed Packet-Carried Forwarding State directly into packet headers to eliminate per-hop lookups.
- Enforce cryptographic path validation to ensure traffic follows only authorized, contracted routes.
Based on Key dates, commercial peering launched with Anapaya at Equinix sites on October 5, 2021. Financial firms secure deterministic latency while ignoring the chaotic behavior of the underlying physical transport. Total isolation conflicts with the need for broad connectivity. Full galvanic separation sacrifices access to the general internet. Networks requiring external reachability must maintain parallel BGP sessions, effectively doubling operational complexity during the transition phase. The limitation appears as reduced route diversity outside the private trust domain. Five distinct challenges emerge when migrating legacy systems to this structured environment.
Deploying Secure Financial Networks with SCION for Low-Latency Trading
SCION's Open-Source Overlay Model and MPLS Integration
SCION deploys as a free, open-source overlay utilizing existing IP or MPLS forwarding fabrics without hardware replacement. RIPE Labs data confirms this architecture requires zero changes to internal domain infrastructure while eliminating licensing fees. The mechanism encapsulates path segments within packet headers, allowing operators to bypass unstable BGP control planes entirely. This approach enables galvanic isolation where financial traffic flows separate from the public internet's volatility. Operational complexity arises when managing dual routing states during migration phases. Most firms overlook that maintaining synchronization between the overlay and underlay demands strict configuration discipline.
Strategic Adoption: National Interest Versus Carrier Cost Drivers
BGP dominance persists because carrier costs drive decisions rather than national interest strategies. Financial institutions evaluating SCION must weigh immediate expense against the strategic imperative of digital sovereignty. The Swiss Federal Council recognized considerable potential for SCION at the federal level for greater data security on 30 October 2025, signaling state-level prioritization over market efficiency. This creates a tension where private banks face pressure to adopt sovereign architectures while competitors optimize purely for margin. Deployment physics limit current capabilities since SCION functions largely as an overlay network depending on BGP as a routing fabric. Operators cannot achieve full isolation without physical asset control, meaning partial deployments inherit underlying instabilities. A decision framework requires mapping criticality: high-frequency trading systems demand the deterministic latency SCION offers, whereas bulk data transfers tolerate BGP variance. InterLIR recommends adoption only when regulatory mandates or latency penalties exceed the operational overhead of managing separate path segments. The cost barrier remains significant despite the software being free, as organizational inertia favors established vendor relationships. Networks ignoring this shift risk obsolescence if geopolitical fragmentation accelerates.
About
Nikita Sinitsyn Customer Service Specialist at InterLIR brings eight years of telecommunications expertise to the discussion on SCION network architecture. While SCION represents a futuristic, BGP-free routing model adopted by Swiss banks, Sinitsyn's daily work addresses the immediate realities of the current internet infrastructure. At InterLIR, a Berlin-based IPv4 marketplace, he manages critical RIPE and ARIN database operations, ensuring clean BGP announcements and reliable IP reputation for clients. This hands-on experience with the complexities and vulnerabilities of traditional routing protocols provides a practical foundation for analyzing why alternatives like SCION are gaining traction in high-security sectors. By navigating the intricacies of IP resource redistribution and spam control, Sinitsyn understands the urgent need for the isolation and control that SCION promises. His perspective bridges the gap between today's operational challenges in IP management and the strategic evolution toward more resilient, next-generation networks essential for global finance.
Conclusion
SCION's promise of galvanic isolation fractures when organizations attempt to scale beyond pilot programs, primarily because the operational debt of maintaining dual routing states often exceeds the theoretical security benefits. While the protocol eliminates licensing fees, the hidden cost lies in the relentless human effort required to synchronize overlay path segments with an unstable BGP underlay. As geopolitical fragmentation accelerates, relying on a hybrid model that inherits public internet volatility becomes a strategic liability rather than a transitional phase. True sovereignty demands physical asset control, not just software encapsulation, meaning partial deployments will fail to deliver the deterministic latency critical for high-frequency trading.
Organizations must commit to a full infrastructure overhaul within the next 18 months if their regulatory exposure or latency penalties justify the intense migration overhead; otherwise, they should remain on optimized BGP to avoid unnecessary complexity. Do not adopt SCION merely for novelty; reserve it for systems where digital sovereignty is non-negotiable and margin optimization is secondary. Start by auditing your current critical path dependencies this week to identify which specific traffic flows would suffer catastrophic financial loss from a mere 50-millisecond BGP fluctuation, as only these candidates warrant the immediate operational disruption of migration.