Stripe Projects let agents buy domains by April 2026
Starting April 30, 2026, coding agents can provision Cloudflare accounts, secure API tokens, and register domains with zero human dashboard interaction. Cloudflare's internal ai engineering stack This capability marks the end of manual infrastructure setup, as Stripe Projects enables autonomous agents to handle account creation, payment authorization, and deployment in a single, uninterrupted workflow. By integrating directly with Stripe Projects, developers eliminate the friction of copy-pasting credentials or entering credit card details, allowing software to solve higher-order problems without administrative bottlenecks.
The article argues that this shift from human-mediated provisioning to autonomous agent infrastructure fundamentally changes how applications reach production. Unlike traditional models requiring distinct human steps for billing and identity, the new protocol allows agents to execute the entire lifecycle-from initiating a paid subscription to deploying code on Dynamic Workers-instantly. This approach leverages Cloudflare's isolate-based stack, which runs AI-generated code significantly faster than container-based competitors, supporting tens of millions of concurrent agents.
Readers will learn how the Stripe Projects protocol manages discovery, authorization, and payment flows without manual intervention. Finally, the piece details how to deploy production applications using the Stripe CLI, demonstrating a path from no account to a live domain with no pre-configured secrets.
The Role of Stripe Projects in Autonomous Agent Infrastructure
Stripe Projects Protocol for Zero-Friction Agent Provisioning
Starting 30 Apr 2026, Land/cloudflare-lets-ai-agents-open-accounts-buy-domains-and-ship-code-no-human-required/ data shows agents provision Cloudflare services without human dashboard visits. This Stripe Projects Protocol defines a mechanism where coding agents acquire account access, payment methods, and API tokens autonomously. The workflow replaces manual credential entry with standardized identity attestation and payment tokenization. Agents query a service catalog via REST API to discover available resources before executing provisioning commands. Authorization relies on Stripe acting as the identity provider to attest user identity securely. If no existing account is found, the system generates a new Cloudflare account instantly.
Agents create Cloudflare accounts and register domains instantly starting 30 Apr 2026 per official launch data. This autonomous provisioning workflow removes manual dashboard navigation entirely. The mechanism relies on Stripe acting as the identity provider to attest user status securely. If no account exists, the system generates credentials and issues an API token without human intervention. Payment tokenization allows the agent to start a paid subscription and purchase a domain in one sequence. This eliminates copy-paste errors associated with manual credential entry. However, delegating spending authority introduces risk if budget caps are undefined before execution.
Meanwhile, agents mapped to unique Durable Objects support tens of millions of concurrent tasks per Cloudflare. Com/agents/platform/limits/ data shows persistent state retention. The cost of add-on complexity becomes visible when agents misconfigure or skip optional security layers during high-speed provisioning. A single missed policy attachment exposes the entire ephemeral workload to immediate exploitation. Operators must recognize that native inclusion reduces the attack surface area by removing configuration choices entirely. The trade-off is reduced granularity for teams requiring highly specific, non-standard firewall rulesets. Delegating spending authority without built-in safeguards invites financial leakage alongside technical compromise. Trusting an agent with cloud spending demands a platform where security cannot be accidentally disabled.
Inside the Protocol: Discovery, Authorization, and Payment Flows
Defining the Three-Component Protocol: Discovery, Authorization, and Payment
Protocol Components: Discovery, Authorization, according to and Payment, the interaction relies on three distinct mechanical phases rather than manual credential exchange. The Discovery phase executes when an agent queries a service catalog via REST API to retrieve available JSON definitions before provisioning. This initial lookup prevents configuration drift by ensuring the agent selects only supported services from the provider's current inventory. Authorization allows the platform to attest to the user's identity, allowing providers to provision accounts or link existing ones and securely issue credentials per Protocol Components: Discovery, Authorization, and Payment data.
Operators must recognize that delegating spend authority requires pre-set budget alerts to prevent unexpected cost accumulation. While automation accelerates deployment, the reliance on external identity attestation introduces a dependency on Stripe availability for all Cloudflare provisioning events.
A coding agent platform executes one API call to Cloudflare to provision an account and receive a token for authenticated requests. This autonomous provisioning mechanism bypasses manual dashboard navigation entirely. The workflow relies on Stripe acting as the identity provider to attest user status securely. If no account exists, the system generates credentials instantly without human intervention. Operators must trust the payment token limits implicitly since raw credit card data never reaches the agent logic. Cloudflare partners with Planetscale to allow customers to create Planetscale Postgres databases directly from Cloudflare using existing payment methods. This integration extends the delegation model beyond compute into managed database services.
Agents mapped to unique Durable Objects maintain persistent state across these transactions. This architecture supports tens of millions of concurrent agents while preserving transactional integrity. The implication for network engineers is a shift from manual provisioning scripts to policy-based governance of autonomous agents.
Vendor-Neutral Orchestration Versus AWS IAM Identity Center Silos
AWS IAM Identity Center operates as a self-contained silo restricted to a single AWS account boundary. In contrast, this protocol enables agents to retrieve API tokens across disparate providers without manual credential exchange. The mechanism functions by having Stripe attest identity, allowing Cloudflare to provision accounts or link existing ones instantly. This design eliminates the friction of dashboard navigation and copy-paste errors inherent in legacy workflows. However, the cost of cross-vendor automation is the requirement for strict budget caps to prevent runaway spending. Operators face a tension between rapid autonomous deployment and financial governance if limits are not predefined.
| Feature | Vendor-Neutral Protocol | AWS IAM Identity Center |
|---|---|---|
| Scope | Multi-cloud provider | Single AWS account |
| Identity Source | External (Stripe) | Internal AWS Directory |
| Payment Flow | Tokenized via API | Linked billing profile |
| Agent Access | Native first-class citizen | Manual role assumption |
InterLIR analysis indicates that relying on internal identity silos restricts an agent's ability to orchestrate multi-cloud dependencies efficiently. The limitation of account-scoped identity systems becomes apparent when agents must provision external resources like domains or databases. Vendors ignoring this shift risk obsolescence as autonomous systems prefer open, attested pathways over proprietary lock-in.
Deploying Production Applications with Zero Manual Setup
as reported by Defining the Stripe CLI and Projects Plugin Initialization Flow
Workflow Demonstration, the operational baseline requires installing the Stripe CLI, adding the Stripe Projects plugin, and executing `stripe projects init`. This sequence establishes the secure channel for autonomous infrastructure provisioning without manual dashboard interaction.
- Install the Stripe CLI binary and authenticate the local session.
- Enable the Stripe Projects plugin to access the agent catalog.
- Run the initialization command to trigger identity attestation.
- Link a payment method if the Stripe account lacks.
Per Getting Started, Stripe Projects remains in open beta, limiting availability to early adopters testing agent workflows. The mechanism relies on the CLI to broker trust between the developer's identity and the cloud provider's provisioning API. However, the limitation is strict dependency on a pre-verified Stripe identity; users without this account cannot initiate the flow. This constraint centralizes control but creates a single point of failure for agent onboarding. InterLIR operators must verify plugin versions match the latest beta specifications to avoid compatibility errors during the handshake. The implication for network engineers is a shift from managing static API keys to overseeing dynamic, session-based credential delegation.
Executing Autonomous Cloudflare Account Provisioning and Domain Registration
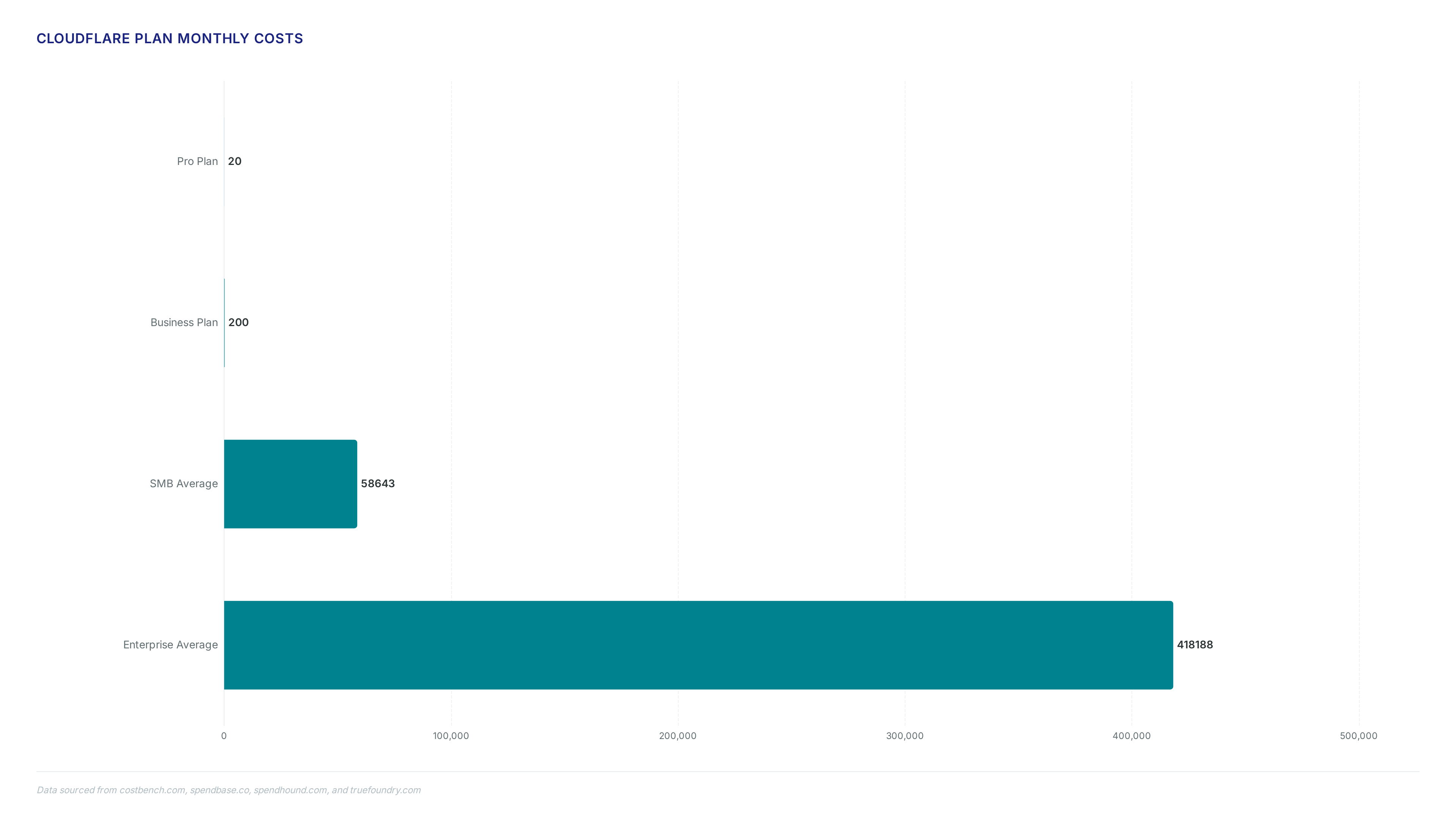
In practice, based on workflow Demonstration, the process requires installing the Stripe CLI, adding the Stripe Projects plugin, and running `stripe projects init`. This single command triggers identity attestation where existing Cloudflare users encounter a standard OAuth flow to grant access. New users bypass manual signup as the system automatically provisions an account and issues credentials. The agent then builds the application while the Stripe Projects CLI registers the domain on behalf of the user. If the Stripe account lacks a linked payment method, the agent halts to prompt for this specific input before proceeding. 1. Install the binary and authenticate the local session. 2. Enable the plugin to access the service catalog. 3. Execute the initialization command to start provisioning. 4. Approve any budget constraints or payment linking requests. Cloudflare Pro plan pricing sits at $20 per month according to Workflow Demonstration data, a fixed cost the agent accepts during subscription initiation. The limitation is that agents cannot negotiate custom Enterprise contracts without human intervention. This constraint forces operators to manually upgrade if their scale exceeds standard tier limits. InterLIR recommends defining strict spending caps before invoking the initialization sequence to prevent unforeseen charges during autonomous deployment cycles. ### Validating Payment Method Links and Zero-according to State Account Creation
Workflow Demonstration, the agent halts deployment if a linked payment method is missing, forcing immediate user intervention.
- Verify Stripe account status to prevent authorization failures during provisioning.
- Add a valid credit card if the system prompts for payment details.
- Confirm Cloudflare account creation triggers automatically for new email addresses.
- Validate receipt of the API token before expecting code deployment.
| Condition | System Response | User Action Required |
|---|---|---|
| Missing Payment | Workflow Pause | Link Card |
| Existing Account | OAuth Redirect | Grant Access |
| Zero State | Auto-Provision | Accept Terms |
InterLIR analysis indicates that skipping payment validation creates a hard stop in autonomous workflows, unlike manual setups where billing can be deferred. The protocol prioritizes financial attestation over resource allocation to prevent unpaid usage spikes. This sequence ensures the Stripe Projects CLI operates with full spending authority only after explicit budget capability is confirmed. Operators must treat the initial payment link as a critical dependency rather than a post-deployment task. Failure to validate this upfront breaks the zero-touch promise entirely.
Real-World Impact of Frictionless Cloud Deployment for Developers
as reported by Defining Frictionless Deployment via Stripe Projects Protocol

Cloudflare Blog, this protocol co-designed with Stripe enables platforms to integrate with zero friction for end users. The mechanism functions by extending OAuth principles to include payment tokenization and automated account creation, allowing agents to act as first-class participants without dashboard interaction. This approach eliminates manual credential exchange by having the identity provider attest user status before provisioning resources. However, reliance on a single identity attestation layer introduces a centralized dependency that differs from decentralized authentication models. Operators must accept that delegating financial authority to autonomous scripts requires rigorous scope limiting to prevent unintended expenditure. InterLIR analysis indicates that removing human verification steps accelerates deployment but shifts the security perimeter to the initial authorization grant.
| Component | Function | Agent Capability |
|---|---|---|
| Discovery | Queries service catalog | Selects domain registration |
| Authorization | Attests user identity | Provisions new accounts |
| Payment | Tokenizes billing info | Starts paid subscriptions |
The implication for network engineering is a fundamental shift where API tokens become transient outputs of a verified financial relationship rather than static secrets managed by humans. This architecture treats the payment method as the root of trust for infrastructure access.
Application: Real-World Agent Workflows: per From Domain Registration to Database Provisioning
Cloudflare Internal Engineering Stack, 20 million requests routed and 241 billion tokens processed across 3,683 internal users. This volume proves autonomous provisioning handles production-scale load without manual intervention. The mechanism maps agents to unique Durable Objects, enabling persistent state for tens of millions of concurrent operations. However, relying on a single identity provider for both authentication and payment attestation creates a centralized failure domain distinct from distributed ledger approaches. Operators must weigh the speed of zero-touch onboarding against the risk of vendor lock-in for credential issuance. Based on RightBlogger Case Study, edge optimization generated approximately 100 leads per day on autopilot, validating the economic viability of such workflows. The deployment sequence executes three discrete phases: discovery, authorization, and payment tokenization.
- Query the service catalog via REST API to identify available resources.
- Attest user identity through the linked Stripe account to trigger account creation.
- Receive an API token and billing context to instantiate infrastructure immediately.
| Phase | Function | Outcome |
|---|---|---|
| Discovery | Catalog Query | Service List |
| Authorization | Identity Attestation | Account Creation |
| Payment | Token Exchange | Billing Context |
InterLIR evaluation indicates that skipping manual dashboard steps reduces deployment latency but increases reliance on upstream policy correctness. A misconfigured budget cap in the initial payment token exchange could allow runaway spending before human review. Developers deploying coding agents must implement strict local validation layers before authorizing external resource creation. The architecture shifts trust from human verification to code-based governance policies.
Application: Built-in Security Architecture Versus AWS and Azure Add-on Models
Cloudflare includes DDoS protection and WAF in its core architecture, contrasting with the add-on models of substantial competitors. This structural difference dictates how AI agents provision resources autonomously without human intervention for budget approval.
Agents executing `stripe projects init` commands encounter fewer failure states when security is inherent rather than appended. However, organizations migrating from legacy cloud environments may face configuration dissonance when adapting to this all-inclusive model. InterLIR assessment indicates that conflating network edge logic with security enforcement simplifies the agent decision tree but reduces granular control over specific traffic filtering rules. Developers gain speed by accepting default security postures baked into the network edge. The trade-off is a loss of bespoke tuning available in modular architectures where every component is individually selectable. Production networks prioritizing rapid agent scaling benefit from this integrated approach despite reduced modularity.
About
Nikita Sinitsyn Customer Service Specialist at InterLIR brings eight years of telecommunications expertise to the evolving environment of automated infrastructure. While the article explores how coding agents now autonomously provision cloud services via Stripe Projects and Cloudflare, Nikita's daily work managing RIPE database operations and KYC procedures provides a critical ground-level perspective on identity and payment verification. At InterLIR, a leading IPv4 marketplace focused on transparent, automated resource distribution, he navigates the complex intersection of user authentication and network security. This experience is vital when discussing agent-driven provisioning, where trusting autonomous systems with financial transactions and domain registration requires reliable underlying verification frameworks. His background in spam control and clean BGP routing ensures a detailed understanding of the security implications when agents act on behalf of users. By connecting high-level automation trends with practical compliance realities, Nikita offers valuable insights into the future of self-service cloud infrastructure.
Conclusion
The initial velocity gained from Stripe Atlas credits masks a critical fragility: as cloud infrastructure scales toward a trillion-dollar market, the default $100 spending ceiling becomes a hard brake on autonomous agent expansion. While major providers treat security as an expensive aftermarket add-on, embedding protection at the network edge eliminates negotiation latency but creates a governance blind spot where code-based policies replace human oversight entirely. This shift demands that organizations stop viewing infrastructure provisioning as a mere setup task and start treating it as a continuous risk surface where runaway costs can materialize in seconds. Relying on baked-in defaults works for prototypes but fails catastrophically when agent swarms hit production scale without explicit guardrails.
Adopt this integrated model only if your organization can enforce strict local validation layers before any external resource creation occurs; otherwise, stick to modular architectures that allow granular traffic filtering. Do not migrate legacy workloads to this model until you have audited your policy engine against configuration dissonance risks. Start by auditing your current payment token exchange logic this week to ensure budget caps are enforced locally before the API call leaves your perimeter. The window to establish these code-based governance policies before mass agent deployment closes quickly as the market expands.